Fraud & Cybersecurity
July 26, 2024: Fraud & Cybersecurity Articles
- How a North Korean Fake IT Worker Tried to Infiltrate Us
- CISA’s Jack Cable Discusses US Push for More Secure Software
- Again?! Combating the Resurgence of the Medusa Banking Trojan
- Google Chrome Now Warns About Risky Password-Protected Archives
How a North Korean Fake IT Worker Tried to Infiltrate Us
Stu Sjouwerman, KnowBe4
 First of all: No illegal access was gained, and no data was lost, compromised, or exfiltrated on any KnowBe4 systems. This is not a data breach notification, there was none. See it as an organizational learning moment I am sharing with you. If it can happen to us, it can happen to almost anyone. Don’t let it happen to you. We wrote an FAQ, answering questions from customers. Story updated 7/25/2024.
First of all: No illegal access was gained, and no data was lost, compromised, or exfiltrated on any KnowBe4 systems. This is not a data breach notification, there was none. See it as an organizational learning moment I am sharing with you. If it can happen to us, it can happen to almost anyone. Don’t let it happen to you. We wrote an FAQ, answering questions from customers. Story updated 7/25/2024.
TLDR: KnowBe4 needed a software engineer for our internal IT AI team. We posted the job, received resumes, conducted interviews, performed background checks, verified references, and hired the person. We sent them their Mac workstation, and the moment it was received, it immediately started to load malware.
Our HR team conducted four video conference based interviews on separate occasions, confirming the individual matched the photo provided on their application. Additionally, a background check and all other standard pre-hiring checks were performed and came back clear due to the stolen identity being used. This was a real person using a valid but stolen US-based identity. The picture was AI “enhanced”.
The EDR software detected it and alerted our InfoSec Security Operations Center. The SOC called the new hire and asked if they could help. That’s when it got dodgy fast. We shared the collected data with our friends at Mandiant, a leading global cybersecurity expert, and the FBI, to corroborate our initial findings. It turns out this was a fake IT worker from North Korea. The picture you see is an AI fake that started out with stock photography (below). The detail in the following summary is limited because this is an active FBI investigation.
SUMMARY: This report covers the investigation of Employee ID: XXXX hired as a Principal Software Engineer. On July 15, 2024, a series of suspicious activities were detected on that user account. Based on the SOC teams evaluation of the activities it was found this may have been intentional by the user and suspected he may be an Insider Threat/Nation State Actor. Upon initial investigation and containment of host, a more detailed inquiry into the new hire took place. Read more
CISA’s Jack Cable Discusses US Push for More Secure Software
James Coker, Infosecurity Magazine
 Cybersecurity researchers have observed a surge in the exploitation of vulnerabilities in widely used software products by both financially-motivated cybercriminals and nation-state actors.
Cybersecurity researchers have observed a surge in the exploitation of vulnerabilities in widely used software products by both financially-motivated cybercriminals and nation-state actors.
As well as being able to gain initial access multiple organizations in a single hit, this approach provides a basis for evading defenses and establishing persistent access in target networks. Incidents like SolarWinds in 2020, Log4j in 2022 and MOVEit in 2023 significantly impacted government and critical sector organizations.
In response to this trend, the White House’s National Cybersecurity Strategy, unveiled in March 2023, aims to shift the security responsibility away from end users to those best placed to shoulder that burden, including software manufacturers. The Cybersecurity and Infrastructure Security Agency (CISA) developed a Secure by Design initiative in April 2023 to explain how software manufacturers can ensure security is built into their products.
A Secure by Design Pledge was then announced in May 2024, encouraging manufacturers to commit to making progress across a range of secure by design principles. Infosecurity Magazine recently spoke to Jack Cable, Senior Technical Advisor at CISA, to find out more about the Secure by Design initiative and pledge and their progress to date. Read more
Again?! Combating the Resurgence of the Medusa Banking Trojan
Anne Saita, The Financial Brand
 The resurgence of the Medusa banking trojan poses a significant threat to Android users in seven countries, stealing financial information through sophisticated methods. Banks and credit unions can protect customers by educating them on detection, removal and prevention strategies, fostering trust and security.
The resurgence of the Medusa banking trojan poses a significant threat to Android users in seven countries, stealing financial information through sophisticated methods. Banks and credit unions can protect customers by educating them on detection, removal and prevention strategies, fostering trust and security.
Just as the gaze of the mythical Medusa turned onlookers to stone, the recent resurgence of the Medusa banking trojan stunned banks and credit unions. Financial institutions continue to field calls from customers fearing they’ve been infected and that their financial assets have been wiped out.
By understanding and conveying the threat and mitigations to all stakeholders, officials at banks and credit unions can safeguard funds and forge a stronger connection with their customers and members.
A Stealthier Banking Trojan Re-emerges
The Medusa banking trojan first surfaced in 2020 to steal sensitive financial information from Android devices. It spread through phishing emails and messages from seemingly trustworthy sources, prompting users to unwittingly download and install the malware that surreptitiously steals banking credentials.
Its developers have continuously updated the trojan, adding sophisticated features like keylogging, screen capturing and remote-control capabilities. This adaptability allowed Medusa to bypass many traditional anti-malware defenses, contributing to its early successes.
One new feature allows the attacker to display a full black screen on the target device, creating the illusion that it is locked or turned off. This acts as camouflage for conducting malicious operations undetected. Read more
Google Chrome Now Warns About Risky Password-Protected Archives
Sergiu Gatlan, Bleeping Computer
 Google Chrome now warns when downloading risky password-protected files and provides improved alerts with more information about potentially malicious downloaded files.
Google Chrome now warns when downloading risky password-protected files and provides improved alerts with more information about potentially malicious downloaded files.
These new, more detailed warning messages help users quickly learn the nature of the danger presented by each file downloaded from the Internet. For this, Google introduced a two-tier download warning system that uses AI-powered malware verdicts sourced from its Safe Browsing service to help evaluate the actual risk quickly.
Users will now see warnings alerting them of suspicious files (based on lower confidence verdicts and unknown risk of user harm) or dangerous files (on high confidence verdicts and high risk of user harm). “These two tiers of warnings are distinguished by iconography, color, and text, to make it easy for users to quickly and confidently make the best choice for themselves based on the nature of the danger and Safe Browsing’s level of certainty,” the Chrome Security team explains.
“Overall, these improvements in clarity and consistency have resulted in significant changes in user behavior, including fewer warnings bypassed, warnings heeded more quickly, and all in all, better protection from malicious downloads.” The Chrome browser now also sends suspicious files to the company’s servers for a deeper scan for users with Enhanced Protection mode enabled in Safe Browsing, providing extra protection while “reducing user friction.” Read more
July 19, 2024: Fraud & Cybersecurity Articles
- How To Tell If Your Online Accounts Have Been Hacked
- Related Reading: How To Protect Your Startup from Email Scams
- Apple Warns iPhone Users in 98 Countries of Spyware Attacks
- BSA Filings and Their Utility to Law Enforcement
- AT&T Breach Linked to American Hacker, Telecom Giant Paid $370k Ransom
How To Tell If Your Online Accounts Have Been Hacked
Lorenzo Franceschi-Bicchierai, TechCrunch
 More and more hackers are targeting regular people with the goal of stealing their crypto, perhaps getting into their bank accounts or simply stalking them. These types of attacks are still relatively rare, so there’s no need for alarm. But it’s important to know what you can do to protect yourself if you suspect someone got into your email or social media account.
More and more hackers are targeting regular people with the goal of stealing their crypto, perhaps getting into their bank accounts or simply stalking them. These types of attacks are still relatively rare, so there’s no need for alarm. But it’s important to know what you can do to protect yourself if you suspect someone got into your email or social media account.
A few years ago, I wrote a guide to help people protect themselves, and understand that most of the companies you have an account with already offer you tools to take control of your accounts’ security, even before you contact them for help, which in some cases you still should do.
Just like in the previous guide, there’s an important caveat. You should know that these methods don’t guarantee that you haven’t been compromised. If you still aren’t sure, you should contact a professional, especially if you are a journalist, a dissident or activist, or otherwise someone who has a higher risk of being targeted. In those cases, the nonprofit Access Now has a digital security helpline that will connect you to one of their experts.
Another caveat, if you don’t do this already, you should enable multi-factor authentication on all your accounts, or at least the most important ones (email, banking, social media). This directory is a great resource that teaches you how to enable multi-factor authentication on more than 1,000 websites. (Note that you don’t have to use the multi-factor app promoted on that site, there are plenty of other alternatives.)
Related Reading: How To Protect Your Startup from Email Scams
Apple Warns iPhone Users in 98 Countries of Spyware Attacks
Manish Singh, TechCrunch
 Apple has issued a new round of threat notifications to iPhone users across 98 countries, warning them of potential mercenary spyware attacks. It’s the second such alert campaign from the company this year, following a similar notification sent to users in 92 nations in April.
Apple has issued a new round of threat notifications to iPhone users across 98 countries, warning them of potential mercenary spyware attacks. It’s the second such alert campaign from the company this year, following a similar notification sent to users in 92 nations in April.
Since 2021, Apple has been regularly sending these notifications, reaching users in over 150 countries, according to a support document on the company’s website. The latest warnings, out Wednesday, did not disclose the attackers’ identities or the countries where users received notifications.
Users in India are among those who have received Apple’s latest threat notifications, according to user testimonials. In October, Apple sent similar warnings to several journalists and politicians in the country. Amnesty International, a human rights advocacy group, later reported discovering the presence of Pegasus, a highly invasive spyware developed by Israeli firm NSO Group, on the iPhones of prominent Indian journalists. Read more
BSA Filings and Their Utility to Law Enforcement
Peter D. Hardy & Siana Danch, MoneyLaundering News
 First in a Two-Part Series on the Utility of BSA Filings
First in a Two-Part Series on the Utility of BSA Filings
Today we are very pleased to welcome guest blogger, Don Fort, who is the Director of Investigations at Kostelanetz LLP, and the past Chief of the Internal Revenue Service’s Criminal Investigation (CI) Division.
As Chief of IRS-CI from 2017 to 2020, Don led the sixth largest U.S. law enforcement agency, managing a budget of over $625 million and a worldwide staff of approximately 3,000, including 2,100 special agents in 21 IRS field offices and 11 foreign countries. Don’s time in law enforcement included overseeing investigations of some of the most significant financial crimes involving tax evasion, sanctions evasion, money laundering, bribery, international corruption, bank malfeasance, cyber and cryptocurrency crimes, and terrorist financing.
We reached out to Don because we were interested in his perspective on the 2023 Year-in-Review (YIR) published by the Financial Crimes Enforcement Network (FinCEN), on which we previously blogged. According to the YIR, there are about 294,000 financial institutions and other e-filers registered to file Bank Secrecy Act (BSA) reports with FinCEN. Collectively, they filed during FY 2023 a total of 4.6 million Suspicious Activity Reports (SARs) and 20.8 million Currency Transaction Reports (CTRs), as well as 1.6 million Reports of Foreign Bank and Financial Accounts (FBARs), 421,500 Forms 8300 regarding cash payments over $10,000 received in a trade or business, and 143,200 Reports of International Transportation of Currency or Monetary Instruments (CMIRs) for certain cross-border transactions exceeding $10,000. Although the YIR necessarily represents only a snapshot lacking full context, only a very small portion of those filings ever became relevant to actual federal criminal investigations. But, the YIR makes clear that one of the most, or the most, important consumers of BSA filings is IRS-CI.
In our next related blog, we will discuss the utility of filings in the global anti-money laundering/countering the financing of terrorism compliance regime, from the perspective of industry – specifically, recent publications by the Wolfsberg Group, and the Bank Policy Institute, the Financial Technology Association, the Independent Community Bankers of America, the American Gaming Association, and the Securities Industry and Financial Markets Association. Read more
AT&T Breach Linked to American Hacker, Telecom Giant Paid $370k Ransom
The massive AT&T breach has been linked to an American hacker living in Turkey, and reports say the telecom giant paid a $370,000 ransom.
Eduard Kovacs, Security Week
 The recently disclosed AT&T data breach has been linked to an American hacker living in Turkey, and the telecom giant reportedly paid a significant ransom to ensure that the stolen information would be deleted.
The recently disclosed AT&T data breach has been linked to an American hacker living in Turkey, and the telecom giant reportedly paid a significant ransom to ensure that the stolen information would be deleted.
AT&T revealed on Friday that it had suffered a data breach affecting nearly all of its wireless customers. The company said that in April hackers exfiltrated records of customer call and text interactions from May 1, 2022, to October 31, 2022, as well as on January 2, 2023. The data originated from AT&T’s ‘workspace’ on a third-party cloud platform.
The company explained that the compromised records identify other phone numbers that impacted customers interacted with, including call or text counts and call durations. The content of calls or texts, timestamps, and other sensitive personal information was not impacted.
“While the data doesn’t include customer names, there are often ways to find a name associated with a phone number using publicly available online tools,” AT&T said. The telecom giant also noted that it does not believe the stolen data is publicly available and said it had received information that “at least one person has been apprehended”. AT&T is notifying roughly 110 million customers about the incident.
More information relating to the AT&T hack became available over the weekend. Wired reported that AT&T paid a hacker roughly $370,000 in bitcoin back in May in order to prevent the data from getting leaked. The hacker in question, a member of the notorious ShinyHunters group, provided proof of the transaction, which was also confirmed to Wired by others based on cryptocurrency transfer records.
The hacker reportedly demanded a $1 million ransom from AT&T, but he ultimately settled for far less. The hacker provided AT&T with a video showing that he had deleted the stolen data.
July 12, 2024: Fraud & Cybersecurity Articles
- Supreme Court Opens Door to More APA Challenges by Ruling that Right of Action Accrues When Regulation First Causes Injury
- RockYou2024: 10 Billion Passwords Leaked In The Largest Compilation of All Time
- Intuit Class Action Claims Co. Failed to Prevent TurboTax, Credit Karma Data Breach
- Hackers Target WordPress Calendar Plugin Used By 150,000 Sites
Supreme Court Opens Door to More APA Challenges by Ruling that Right of Action Accrues When Regulation First Causes Injury
 Opinion Can Invite New Challenges to Long-Standing BSA/AML Regulations
Opinion Can Invite New Challenges to Long-Standing BSA/AML Regulations
Kristen E. Larson, John Culhane, Alan Kaplinsky & Peter D. Hardy, Ballard Spahr
On July 1, 2024, the Supreme Court issued its opinion in Corner Post, Inc. v Board of Governors of the Federal Reserve System in which the Court determined when a Section 702 claim under the Administrative Procedure Act (APA) to challenge a final agency action first accrues. In a 6-3 Opinion, the Supreme Court sided with Corner Post in holding that a right of action first accrues when the plaintiff has the right to assert it in court—and in the case of the APA, that is when the plaintiff is injured by final agency action.
This ruling could open the litigation floodgates for industry newcomers to challenge longstanding agency rules. These APA challenges will be further aided by the Supreme Court’s recent overruling of Chevron deference, giving the courts the power to interpret statutes without deferring to the agency’s interpretation.
This development is relevant to potential challenges to anti-money laundering (“AML”) regulations promulgated under the Bank Secrecy Act (“BSA”) or other statutory schemes by the Financial Crimes Enforcement Network, the federal functional regulators, the Securities Exchange Commission, and FINRA. Many BSA/AML regulations were promulgated many years ago. Historically, litigation challenges to BSA/AML regulations have been rare. Given the combined effect of recent rulings by the Supreme Court, that could change.
Background
This case involves a convenience store merchant, Corner Post, Inc., that opened its truck stop business in 2018. In 2021, Corner Post sued the Federal Reserve Board seeking to invalidate Regulation II, which the FRB enacted 10 years before to cap interchange fees charged by debit card issuers. Without reaching the merits of the complaint, the district court dismissed the case as time-barred and ruled that the six-year statute of limitations for bringing facial APA claims (28 U.S.C. § 2401(a)) begins to run when a final rule is issued. Read more
RockYou2024: 10 Billion Passwords Leaked In The Largest Compilation of All Time
Vilius Petkauskas, CyberNews
 The largest password compilation with nearly ten billion unique passwords was leaked on a popular hacking forum. The Cybernews research team believes the leak poses severe dangers to users prone to reusing passwords.
The largest password compilation with nearly ten billion unique passwords was leaked on a popular hacking forum. The Cybernews research team believes the leak poses severe dangers to users prone to reusing passwords.
The king is dead. Long live the king. Cybernews researchers discovered what appears to be the largest password compilation with a staggering 9,948,575,739 unique plaintext passwords. The file with the data, titled rockyou2024.txt, was posted on July 4th by forum user ObamaCare.
While the user registered in late May 2024, they have previously shared an employee database from the law firm Simmons & Simmons, a lead from an online casino AskGamblers, and student applications for Rowan College at Burlington County.
The team cross-referenced the passwords included in the RockYou2024 leak with data from Cybernews’ Leaked Password Checker, which revealed that these passwords came from a mix of old and new data breaches.
“In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world. Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks,” researchers said. Read more
Intuit Class Action Claims Co. Failed to Prevent TurboTax, Credit Karma Data Breach
Anne Bucher, Top Class Actions
 Intuit class action lawsuit overview:
Intuit class action lawsuit overview:
- Who: Plaintiff Joseph Garite filed a class action lawsuit against Intuit Inc.
- Why: Intuit allegedly failed to adequately safeguard sensitive data which was compromised in a TurboTax and Credit Karma data breach disclosed in March 2024.
- Where: The TurboTax data breach class action lawsuit was filed in California federal court.
Intuit Inc. failed to adequately protect its computer systems, leaving sensitive data vulnerable to a TurboTax and Credit Karma data breach earlier this year, according to a new class action lawsuit.
Plaintiff Joseph Garite alleges Intuit, the maker of popular software services including TurboTax, Credit Karma, Quickbooks and Mailchimp, failed to maintain reasonable security safeguards and failed to adequately train employees about cybersecurity.
Hackers Target WordPress Calendar Plugin Used By 150,000 Sites
Bill Toulas, Bleeping Computer
Hackers are trying to exploit a vulnerability in the Modern Events Calendar WordPress plugin that is present on more than 150,000 websites to upload arbitrary files to a vulnerable site and execute code remotely. The plugin is developed by Webnus and is used to organize and manage in-person, virtual, or hybrid events.
The vulnerability exploited in attacks is identified as CVE-2024-5441 and received a high-severity score (CVSS v3.1: 8.8). It was discovered and reported responsibly on May 20 by Friderika Baranyai during Wordfence’s Bug Bounty Extravaganza.
In a report describing the security issue, Wordfence says that the security issue stems from a lack of file type validation in the plugin’s ‘set_featured_image’ function, used for uploading and setting featured images for the events. The function takes an image URL and post ID, tries to get the attachment ID, and if not found, downloads the image using the get_web_page function.
It retrieves the image using wp_remote_get or file_get_contents, and saves it to the WordPress uploads directory using file_put_contents function. Modern Event Calendar versions up to and including 7.11.0 have no checks for the file type of extension in uploaded image files, allowing any file type, including risky .PHP files, to be uploaded. Read more
June 28, 2024: Fraud & Cybersecurity Articles
- Evolve Data Breach Adds to Woes of Synapse Partner
- New AML Rules Will Change the EU’s Financial Crime Prevention Landscape for Good. But What Will Change in Practice?
- SolarWinds Serv-U Vulnerability Under Active Attack – Patch Immediately
- Leader of Money Laundering and Bank Fraud Ring Sentenced to Seven Years in Prison
Evolve Data Breach Adds to Woes of Synapse Partner
Customer data was released to the dark web, the bank said Wednesday, two weeks after the Fed handed Evolve an enforcement action regarding its partnerships.
Dan Ennis, Banking Dive
 Evolve Bank & Trust customer data has been breached, the company confirmed Wednesday in a statement on its website. “A known cybercriminal organization … appears to have illegally obtained and released on the dark web the data and personal information of some Evolve customers,” the bank said.
Evolve Bank & Trust customer data has been breached, the company confirmed Wednesday in a statement on its website. “A known cybercriminal organization … appears to have illegally obtained and released on the dark web the data and personal information of some Evolve customers,” the bank said.
Debit cards, online and digital banking credentials of the firm’s retail-banking customers have not been affected, Evolve said in an update. But the bank is notifying customers of its fintech partners, it said. Evolve did not name the hacking organization, but Bloomberg reported Wednesday that LockBit 3.0 posted data taken from Evolve’s systems on the dark web a day earlier.
Affected information “may have included full name, account number, email address, mailing address, phone number, Social Security number [and] date of birth,” Evolve wrote in its statement. The bank is offering affected customers complimentary credit monitoring services with identity theft monitoring, it said. It did not detail how many customers are affected.
Evolve is communicating with law enforcement to help with an investigation of the matter, the bank said. “Based on what our investigation has found and what we know at this time, we are confident this incident has been contained and there is no ongoing threat,” Evolve said. Read more
New AML Rules Will Change the EU’s Financial Crime Prevention Landscape for Good. But What Will Change in Practice?
Alexandra Jour-Schroeder, European Union
 On 24 April, the European Parliament formally endorsed the future Anti-Money Laundering Package, a reform that has been in the making for the past 5 years. Since the European Commission published its proposals in July 2021, and even before, much has been said about how this reform will change the EU’s financial crime prevention landscape for good.
On 24 April, the European Parliament formally endorsed the future Anti-Money Laundering Package, a reform that has been in the making for the past 5 years. Since the European Commission published its proposals in July 2021, and even before, much has been said about how this reform will change the EU’s financial crime prevention landscape for good.
But how will things change in practice? Here are a few simple examples!
Real estate
Criminals often channel money into super fancy mansions and estates. Until now, only information about EU owners has been available to investigative authorities. When the property is owned by a company in a non-EU country, it is extremely hard to identify whether it may have been acquired with illicit funds. The new rules require foreign companies, as well as trusts, that have owned a piece of real estate in the EU since 2014 to record in our beneficial ownership registers who the individuals who own or control the company or trust are. Member States can put the reference date further back in the past, if they consider that certain risks make this necessary.
Cash
As the sudden peak in online fraud during the pandemic showed, criminals do not suffer from any kind of digital divide. Yet, any investigator would tell you that of all the means that exist to launder illicit proceeds, cash remains criminals’ preferred choice. Why? Because it’s easy to transfer, fully anonymous and therefore difficult, if not impossible, to trace back to some criminal act. Of course, access to cash is and will remain a right for everybody in the EU and most cash transfers are absolutely clean. The continued acceptance and availability of cash is an important issue for our consumers, including for financial inclusion. Read more
SolarWinds Serv-U Vulnerability Under Active Attack – Patch Immediately
The Hacker News
 A recently patched high-severity flaw impacting SolarWinds Serv-U file transfer software is being actively exploited by malicious actors in the wild.
A recently patched high-severity flaw impacting SolarWinds Serv-U file transfer software is being actively exploited by malicious actors in the wild.
The vulnerability, tracked as CVE-2024-28995 (CVSS score: 8.6), concerns a directory transversal bug that could allow attackers to read sensitive files on the host machine. Affecting all versions of the software prior to and including Serv-U 15.4.2 HF 1, it was addressed by the company in version Serv-U 15.4.2 HF 2 (15.4.2.157) released earlier this month.
The list of products susceptible to CVE-2024-28995 is below –
- Serv-U FTP Server 15.4
- Serv-U Gateway 15.4
- Serv-U MFT Server 15.4, and
- Serv-U File Server 15.4
Security researcher Hussein Daher of Web Immunify has been credited with discovering and reporting the flaw. Following the public disclosure, additional technical details and a proof-of-concept (PoC) exploit have since been made available.
Cybersecurity firm Rapid7 described the vulnerability as trivial to exploit and that it allows external unauthenticated attackers to read any arbitrary file on disk, including binary files, assuming they know the path to that file and it’s not locked. Read more
Leader of Money Laundering and Bank Fraud Ring Sentenced to Seven Years in Prison
U.S. Attorney’s Office, Southern District of New York
 Damian Williams, the United States Attorney for the Southern District of New York, announced that ADEDAYO JOHN was sentenced today by U.S. District Judge Loretta A. Preska to seven years in prison for his role as a leader of a money laundering and bank fraud ring that laundered millions of dollars in proceeds derived from business email compromises and romance fraud schemes impacting more than 50 victims. JOHN previously pled guilty to one count of conspiracy to commit money laundering and one count of conspiracy to commit bank fraud on January 4, 2024. In total, 11 defendants have pled guilty for their roles in the money laundering and bank fraud schemes.
Damian Williams, the United States Attorney for the Southern District of New York, announced that ADEDAYO JOHN was sentenced today by U.S. District Judge Loretta A. Preska to seven years in prison for his role as a leader of a money laundering and bank fraud ring that laundered millions of dollars in proceeds derived from business email compromises and romance fraud schemes impacting more than 50 victims. JOHN previously pled guilty to one count of conspiracy to commit money laundering and one count of conspiracy to commit bank fraud on January 4, 2024. In total, 11 defendants have pled guilty for their roles in the money laundering and bank fraud schemes.
Victims were typically defrauded in one of two ways. In some instances, business email compromise fraud schemes were used to trick businesses into transferring funds to bank accounts the victims believed were under the control of legitimate recipients of the funds as part of normal business operations, when in fact the bank accounts were under the control of the defendants or their co-conspirators. In other instances, romance scams were used, primarily through electronic messages sent via email, text messaging, social media, or online dating websites, to deceive victims – many of whom were older men and women – into believing they were in romantic relationships with fake identities, and then using false pretenses to cause the victims to transfer funds to bank accounts controlled by the defendants or their co-conspirators.
As a result of these frauds, law enforcement officers have identified transfers of more than $19 million into bank accounts under the control of the defendants. Read more
June 21, 2024: Fraud & Cybersecurity Articles
- 7 Warning Signs Your Computer Has Been Hacked — And What to Do
- Swiss Regulator Finds HSBC Violated Money Laundering Rules
- Security Bug Allows Anyone to Spoof Microsoft Employee Emails
- Dallas-Based Frontier Communications Hit with Multiple Class Action Lawsuits
7 Warning Signs Your Computer Has Been Hacked — And What to Do
If something doesn’t seem right, it’s time to run some scans.
Chris Hoffman, PC World
 Your antivirus will protect you from many online threats, but no antivirus is perfect. Truth is, your PC can still be hacked even if you’re using reputable security software with a solid track record. When we talk about your computer possibly being “hacked,” that’s exactly what we mean: a cybercriminal has gained access to your PC and compromised it in some way.
Your antivirus will protect you from many online threats, but no antivirus is perfect. Truth is, your PC can still be hacked even if you’re using reputable security software with a solid track record. When we talk about your computer possibly being “hacked,” that’s exactly what we mean: a cybercriminal has gained access to your PC and compromised it in some way.
The hacker in question may be a criminal organization that’s installing malware on millions of PCs (e.g., to spy on you and steal your credit card numbers), or the hacker may be an individual using a remote access Trojan (RAT) to personally spy on you through your webcam.
Here some common warning signs that your PC might’ve been hacked, exposing your personal data and system resources.
Is something fishy? Run an antivirus scan
First things first: If you’re concerned that your computer has a virus or another type of malware, you should run a scan with an antivirus program—ideally one of our recommended antivirus software picks.
You should also consider using the free Norton Power Eraser (or a similar tool). Tools like this will reboot your PC into a special scanning environment outside of Windows so they can spot and remove malware like rootkits that normally evade detection. Perhaps you’ve already run a scan. If your scan didn’t find anything wrong but you’re still concerned, I recommend getting a second opinion. Read more
Swiss Regulator Finds HSBC Violated Money Laundering Rules
Finma bans bank’s Swiss subsidiary from taking on prominent public figures as clients
Owen Walker, Financial Times
 Switzerland’s financial regulator has banned HSBC’s Swiss private bank from taking on prominent public figures as clients after finding the lender violated anti-money laundering regulations.
Switzerland’s financial regulator has banned HSBC’s Swiss private bank from taking on prominent public figures as clients after finding the lender violated anti-money laundering regulations.
Finma imposed a range of penalties on HSBC’s subsidiary in relation to a case that involved several transactions between 2002 and 2015 in which more than $300mn was transferred between Lebanon and Switzerland.
HSBC failed to notify authorities about the transactions until September 2020, despite closing the accounts down in 2016 because of the risks of maintaining the relationships.
“In its checks, the bank failed to recognise the indications of money laundering presented by these transactions; it likewise failed to satisfy requirements for the initiation and continuation of customer relationships with politically exposed persons, and was thus in serious breach of its due diligence obligations,” Finma said.
As part of the sanctions handed down on Tuesday, Finma ordered HSBC to carry out an anti-money laundering review of all its high-risk relationships and business dealings withprominent public clients, known as politically exposed persons. Finma said the bank couldnot start new relationships with PEPs until it had completed its review. Finma and HSBC declined to name the former clients involved in the case. Read more
Security Bug Allows Anyone to Spoof Microsoft Employee Emails
Lorenzo Franceschi-Bicchierai, Tech Crunch
 A researcher has found a bug that allows anyone to impersonate Microsoft corporate email accounts, making phishing attempts look credible and more likely to trick their targets.
A researcher has found a bug that allows anyone to impersonate Microsoft corporate email accounts, making phishing attempts look credible and more likely to trick their targets.
As of this writing, the bug has not been patched. To demonstrate the bug, the researcher sent an email to TechCrunch that looked like it was sent from Microsoft’s account security team.
Last week, Vsevolod Kokorin, also known online as Slonser, wrote on X (formerly Twitter) that he found the email-spoofing bug and reported it to Microsoft, but the company dismissed his report after saying it couldn’t reproduce his findings. This prompted Kokorin to publicize the bug on X, without providing technical details that would help others exploit it.
“Microsoft just said they couldn’t reproduce it without providing any details,” Kokorin told TechCrunch in an online chat. “Microsoft might have noticed my tweet because a few hours ago they reopen [sic] one of my reports that I had submitted several months ago.”
The bug, according to Kokorin, only works when sending the email to Outlook accounts. Still, that is a pool of at least 400 million users all over the world, according to Microsoft’s latest earnings report. Read more
Dallas-Based Frontier Communications Hit with Multiple Class Action Lawsuits
Nadia El-Yaouti, Law Commentary
 The Dallas-based company Frontier Communications is facing at least six class action lawsuits after it was hit with a cyber data breach attack in April. The widespread attack resulted in the personally identifiable information (PII) of over 750,000 customers being stolen by the criminal ransomware group RansomHub. Nearly 90,000 of those victims are Texans.
The Dallas-based company Frontier Communications is facing at least six class action lawsuits after it was hit with a cyber data breach attack in April. The widespread attack resulted in the personally identifiable information (PII) of over 750,000 customers being stolen by the criminal ransomware group RansomHub. Nearly 90,000 of those victims are Texans.
Three of those lawsuits were filed in the Northern District of Texas earlier this month and accused the business of not doing enough to safeguard and properly maintain its network systems and databases. As a result of the company’s negligence and recklessness, the plaintiffs say that they and other victims are now more susceptible to identity theft. One lawsuit maintains that “Frontier knew or should have known that its electronic records would be targeted by cybercriminals.”
Frontier detected the attack on April 14 when the IT department noted abnormal activity on the company’s networks. According to RansomHub, Frontier ignored contact from the criminal group for nearly two months. The contact was likely to demand a ransom payment in exchange for the stolen data. After Frontier ignored and failed to comply with the demand, the criminal group published the stolen data. Among the data were names, birthdates, social security numbers, addresses, and other personal information.
Frontier disclosed that it was the victim of a cyberattack to the Securities and Exchange Commission (SEC) in May. Under the SEC’s disclosure rules, companies are required to report cybersecurity incidents within four business day. Read more
June 14, 2024: Fraud & Cybersecurity Articles
- Alarming Cybersecurity Stats: What You Need to Know in 2024
- City of Cleveland Scrambling to Restore Systems Following Cyberattack
- Frontier Hackers Threaten to Release Private Data For At Least 750,000 Customers
- National Internet Safety Month: This June, Take 4 Easy Steps to Stay Safe Online
Alarming Cybersecurity Stats: What You Need to Know in 2024
Chuck Brooks, Forbes
 There is no doubt that 2023 was a tough year for cyber security. The amount of data breaches keeps rising from previous years, which was already very scary. An exponential rise in the complexity and intensity of cyberattacks like social engineering, ransomware, and DDOS attacks was also seen. This was mostly made possible by hackers using AI tools.
There is no doubt that 2023 was a tough year for cyber security. The amount of data breaches keeps rising from previous years, which was already very scary. An exponential rise in the complexity and intensity of cyberattacks like social engineering, ransomware, and DDOS attacks was also seen. This was mostly made possible by hackers using AI tools.
The last few years have seen a steady rise in the cost of breaches. By letting people work from home, companies created new security holes that hackers can use from their home offices. These holes made the cyber-attack area much bigger.
In addition, the prevalence of malware, and hackers in all commercial verticals has made everyone connected to the internet more susceptible to being breached. There are just too many criminal adversaries and too many entry points available to be reined in and mitigated. Unfortunately, in 2024, the cyber statistics will continue to remain alarming.
Most businesses lack a clear AI adoption roadmap: McKinsey.
Usage has doubled among businesses in the last year, but CIOs still have a laundry list of to-do’s to prepare the tech foundation and governance structure.
- “Generative AI adoption in the workplace is on the rise, but organizations aren’t equipped to guide usage adequately, according to a McKinsey global survey published Thursday. The company surveyed 1,363 organizations, 878 of which regularly use generative AI in at least one function.
- While generative AI high performers are more likely to adhere to best practices, around 3 in 4 nonleading businesses lack an enterprise wide roadmap for generative AI, the report found. Less than 2 in 5 respondents said senior leaders understand how the technology can create value for the business.” Read more
City of Cleveland Scrambling to Restore Systems Following Cyberattack
Ionut Arghire, Security Week
The City of Cleveland is struggling to restore certain services that have been affected by a cyberattack earlier this week.
 The incident was disclosed on June 10, when the city announced that it took its systems offline as a containment measure.
The incident was disclosed on June 10, when the city announced that it took its systems offline as a containment measure.
“City Hall and Erieview are closed today June 10, except for essential staff, as we investigate a cyber incident. We have shut down affected systems to secure and restore services. Emergency services and utilities are not affected. Updates will be provided as available,” the city announced on X.
While Cleveland re-opened both the City Hall and its satellite offices at Erieview Plaza on Wednesday, it decided to close the City Hall again for the remainder of the week, as it continues to work on restoring shut-down systems. “City services will not be available to the public at City Hall tomorrow, June 13 and Friday, June 14. City Hall will be open for employees,” Cleveland announced, advising the public to wait for further information on when services will be restored.
The city said it has been working with key partners to investigate the nature and scope of the incident, noting that taxpayer information held by the CCA and customer information held by Public Utilities are confirmed to have not been affected by the attack. Cleveland also announced that basic city services, including emergency services, public works, public utilities, airport, and online payments were not affected. The Municipal Courts continued to function normally, as they are on a different system.
“Residents are encouraged to use online services or call 311 for more information. We ask for the public’s patience as the city continues its effort to restore system access and broadly recover from the incident in a safe and strategic manner,” Cleveland said. The city shared no information on the identity of the attackers or on whether file-encrypting ransomware was used, albeit taking systems offline is the typical response to a ransomware attack.
Frontier Hackers Threaten to Release Private Data For At Least 750,000 Customers
Jess Weatherbed, the Verge
 Frontier Communications has revealed that information for over 750,000 customers — including full names and Social Security numbers — was exposed in a data breach following a cyberattack on April 14th. Hackers claim to have even more and will release it unless Frontier pays a ransom.
Frontier Communications has revealed that information for over 750,000 customers — including full names and Social Security numbers — was exposed in a data breach following a cyberattack on April 14th. Hackers claim to have even more and will release it unless Frontier pays a ransom.
The attack enabled hackers to access 751,895 customers’ personal data on Frontier’s systems according to a sample of the notice Frontier submitted to the Office of the Maine Attorney General. Frontier has notified impacted customers and provided them with one year of free credit monitoring and identity theft services, but says it “does not believe” customer financial information was exposed in the breach.
Bleeping Computer reports that the RansomHub extortion group claimed responsibility for the attack on June 4th and is threatening to leak the 5GB of customer data it allegedly stole unless Frontier responds to their demands by June 14th. The group claims the stolen dataset contains information belonging to two million Frontier customers, including their full name, physical address, date of birth, social security number, email address, credit score, and phone number.
Frontier says it’s bolstered its network security following the attack and notified both regulatory authorities and law enforcement. A securities filing reveals that the company was forced to shut down some of its systems to contain the incident.
The Verge’s Tom Warren and David Pierce discuss the announcements from Microsoft’s Surface event, including the new Arm-powered Surface Laptop, and Copilot Plus PCs. Verge senior AI reporter Kyle Robison joins the show to chat about OpenAI’s GPT-4o demo and where we’re headed in the next few years of AI. Nilay Patel answers a question about iPads for this week’s Vergecast Hotline.
National Internet Safety Month: This June, Take 4 Easy Steps to Stay Safe Online
By Trent Frazier, Deputy Assistant Director, CISA Stakeholder Engagement Division
 The U.S. Senate first designated June as National Internet Safety Month in 2005, primarily to raise awareness of internet dangers and highlight the need for education about online safety, especially among young people. In the years since then, with the rise of smartphones, social media and other new technologies, the amount of time people spend online has grown enormously—as have the risks.
The U.S. Senate first designated June as National Internet Safety Month in 2005, primarily to raise awareness of internet dangers and highlight the need for education about online safety, especially among young people. In the years since then, with the rise of smartphones, social media and other new technologies, the amount of time people spend online has grown enormously—as have the risks.
Yet, as data from numerous studies show, the nation needs more education and training about the risks we face online and how to stay safe when using connected devices.
Most of the time, cyberattacks occur due to poor cyber hygiene…the basics. Fortunately, there are four simple things we can all do to help protect ourselves and, by extension, others:
- Use strong passwords. “Strong” means at least 16 characters, random, and unique to each account. Use a password manager to automatically generate, store, and fill in passwords for you.
- Turn on multifactor authentication (MFA). MFA provides an extra layer of security in addition to a password when logging into accounts and apps, like a fingerprint, a code from an authenticator app, or a code sent to your phone. Enable it on any account that offers it, especially your email, social media, and financial accounts.
- Update software. When devices, apps, or software programs notify us that updates are available, install them as soon as possible. Updates fix security risks to better protect our data. Turn on automatic updates to make it even easier.
- Recognize and report phishing. Learn to recognize signs of phishing—messages designed to trick you into downloading malware (malicious programs) or giving personal information to a criminal. If an offer is too good to be true, it’s probably social engineering. If the message is alarming and requires urgent action, it might be a phishing message. Do not click or engage—report the phish and delete the message.
CISA offers a variety of free resources to implement these steps and spread the word to friends and family. Our new cybersecurity awareness program Secure Our World provides many resources for improving online safety, such as short how-to videos on the four actions above, tip sheets in 10 languages, and more.
As the school year ends, take this opportunity to discuss the importance of these basic precautions with family and friends. You wouldn’t drive your car without buckling your seatbelt. I buckle my seatbelt so I can be safe. I ask passengers to do the same so they can be safe. If you take these four easy steps to better cyber hygiene when online, your family and the devices you use every day will be much safer and ready for summer fun in just a few minutes.
June 7, 2024: Fraud & Cybersecurity Articles
- Hackers Claim to Have Bank Account Details of 30M Santander Customers
- Google Chrome Deadline—72 Hours to Update or Delete Your Browser
- U.S. Dismantles World’s Largest 911 S5 Botnet with 19M Infected Devices
Hackers Claim to Have Bank Account Details of 30M Santander Customers
FinExtra
 Hackers are trying to sell what they claim are the bank account details of 30 million Santander customers for $2 million.
Hackers are trying to sell what they claim are the bank account details of 30 million Santander customers for $2 million.
Earlier this month, Santander confirmed that a data breach at a third party provider had exposed some client and employee data.
Now, in a post on a hacking forum, the ShinyHunters gang is offering to sell a trove of data, including 30 million bank account details; 28 million credit card numbers; six million account numbers and balances; and HR information on the bank’s 200,000 staffers.
The asking price is $2 million, says the post, adding: “Santander is also very welcome if they want to buy this data.” Earlier this week, the ShinyHunters hackers also claimed responsibility for an attack on TicketMaster. They have previously hit telco AT&T.
However, according to the BBC, experts are urging caution, suggesting that the TicketMaster sale may have been a stunt to bring attention to a new hacking forum replacing one that the police had taken down.
In a statement on the attack two weeks ago, Santander said a bank database hosted by a third party had been accessed. The breach, it said, affected operations in Spain, Chile and Uruguay.
Added the bank: “No transactional data, nor any credentials that would allow transactions to take place on accounts are contained in the database, including online banking details and passwords. The bank’s operations and systems are not affected, so customers can continue to transact securely.”
Related Reading:
- Data Breach at Debt Collector Affects More Than 3.2M People
- Data Breach Involving Millions of Ticketmaster User Accounts Under Investigation
Google Chrome Deadline—72 Hours to Update or Delete Your Browser
Zak Doffman, Forbes
 For Google Chrome and its 2 billion-plus desktop users, May will go down as a month to forget: four zero-days and emergency update warnings inside 10 days launched a tidal wave of wall-to-wall headlines that were hard to miss.
For Google Chrome and its 2 billion-plus desktop users, May will go down as a month to forget: four zero-days and emergency update warnings inside 10 days launched a tidal wave of wall-to-wall headlines that were hard to miss.
The U.S. government has warned federal employees to install May’s emergency updates or to cease using Chrome. They issued a June 3 deadline for the first of those updates to be applied and a June 6 update for the second. June 3 has now passed, and so you should have already applied the first update. This is a timely reminder that you must ensure you have applied the second update within the next 72 hours. Clearly, when you update your browser, all fixes to that point will be applied.
Others organizations should do the same and mandate full employee compliance, as should personal users. Google rushed out emergency fixes for a reason. The U.S. government warnings come via its Cybersecurity and Infrastructure Security Agency, adding May’s Chrome warnings to its Known Exploited Vulnerabilities (KEV) catalog, which details “vulnerabilities that have been exploited in the wild.”
It looks like June 3 has been a significant day all round for Chrome. Not only was that the U.S. government’s first update cutoff, but it’s also the day Google started to pull the plug on many Manifest V2 extensions as its rollout of Manifest V3 takes shape.
While this will affect multiple developers and enterprises, headlines have focused on the detrimental effect this will have on ad blockers, which will need to adopt a complex workaround to work as now. There is a risk that users reading those headlines might seek to delay updating their browser, to prevent any ad blocker issues; you really shouldn’t go down this road—the security update is critical. Read more
The Hacker Newsroom
 The U.S. Department of Justice (DoJ) on Wednesday said it dismantled what it described as “likely the world’s largest botnet ever,” which consisted of an army of 19 million infected devices that was leased to other threat actors to commit a wide array of offenses.
The U.S. Department of Justice (DoJ) on Wednesday said it dismantled what it described as “likely the world’s largest botnet ever,” which consisted of an army of 19 million infected devices that was leased to other threat actors to commit a wide array of offenses.
The botnet, which has a global footprint spanning more than 190 countries, functioned as a residential proxy service known as 911 S5. A 35-year-old Chinese national, YunHe Wang, was arrested in Singapore on May 24, 2024, for creating and acting as the primary administrator of the illegal platform from 2014 to July 2022.
Wang has been charged with conspiracy to commit computer fraud, substantive computer fraud, conspiracy to commit wire fraud, and conspiracy to commit money laundering. If convicted on all counts, Wang faces a maximum penalty of 65 years in prison.
The Justice Department said the botnet was used to carry out cyber attacks, financial fraud, identity theft, child exploitation, harassment, bomb threats, and export violations.
It’s worth noting that Wang was identified as the proprietor of 911 S5 by security journalist Brian Krebs in July 2022, following which the service abruptly shut down on July 28, 2022, citing a data breach of its key components.
Although it was resurrected under a different brand name called CloudRouter a few months later, according to Spur, the service has since ceased operations sometime this past weekend, the cybersecurity company’s co-founder Riley Kilmer told Krebs. Read more
May 31, 2024: Fraud & Cybersecurity Articles
- Google’s New AI Search Goes Horribly Wrong—M Is for Malware
- Alleged Ticketmaster Data Breach Sees 560M Users’ Info for Sale in Hacking Forum
- The Escalating Threat of Mortgage Fraud
- Inside a Zelle Fraud That Almost Lost a Florida Consumer $3,500
Google’s New AI Search Goes Horribly Wrong—M Is for Malware
Zak Doffman, Forbes
 Be careful what you search for—that’s the message, as Google’s new AI search suddenly delivers up a nasty menu of dangerous malware and scams…
Be careful what you search for—that’s the message, as Google’s new AI search suddenly delivers up a nasty menu of dangerous malware and scams…
Well, this is awkward. As the world waits to see the transition from traditional search to the newer, sparklier, more exciting AI alternative, the first update out the traps is not what we expected and appears to have gone horribly wrong.
Google wants to “supercharge search with generative AI,” and has launched its new SGE—or Search Generative Experience to give users an early taste of how this more powerful, contextual mechanism will transform boring old search results.
But last week, one SEO consultant playing with the new technology discovered pretty obvious scams within the results. Bleeping Computer confirmed the results, warning that “Google’s new AI-powered ‘Search Generative Experience’ algorithms recommend scam sites that redirect visitors to unwanted Chrome extensions, fake iPhone giveaways, browser spam subscriptions, and tech support scams.”
And the issue with generative AI, of course, is that dangers come dressed up in nice, friendly, chatty language to which we have not yet honed our defenses.
Google told Bleeping Computer that “we continue to update our advanced spam-fighting systems to keep spam out of Search, and we utilize these anti-spam protections to safeguard SGE.” They also confirmed that “we’ve taken action under our policies to remove the examples shared, which were showing up for uncommon queries.” I have approached Google for any further comments on these issues. Read more
Alleged Ticketmaster Data Breach Sees 560M Users’ Info for Sale in Hacking Forum
Aldohn Domingo, Tech Times
 Ticketmaster has reportedly been breached by the hacking group ShinyHunters, as claimed by the group. The breach compromises the sensitive data of 560 million users, as it is currently on sale for $500,000 in a hacking forum.
Ticketmaster has reportedly been breached by the hacking group ShinyHunters, as claimed by the group. The breach compromises the sensitive data of 560 million users, as it is currently on sale for $500,000 in a hacking forum.
Allegedly, ShinyHunters gained access to many private user data, including complete names, email addresses, phone numbers, addresses, order information, and partial credit card information. The last four digits of credit card numbers, expiration dates, customer names, and even information on customer fraud are among the specific payment data exposed.
If confirmed, the data breach might have serious repercussions for the impacted users, including the possibility of identity theft, financial fraud, and other cyberattacks. The hacker gang’s daring move to sell this data further demonstrates the threat that cybercrime poses and the increasing sophistication of these adversaries.
According to the infamous hacker collective ShinyHunters, Ticketmaster-Live Nation’s security was broken, exposing the personal information of an astounding 560 million members. Now, Breach Forums is offering this enormous 1.3 terabyte of data for a one-time sale of $500,000.
Ticketmaster, the US-based ticket-selling company, could potentially be another major firm this month to confirm it suffered a data breach within its systems. Read more
The Escalating Threat of Mortgage Fraud
Joe Wilson & Sarah Atkinson, Financial Services Perspectives
 Overview
Overview
Mortgage companies must maintain a heightened level of vigilance when it comes to preventing mortgage fraud. The incidence of fraud attempts targeting mortgage companies continues to rise, prompting decisive action against this threat. In a criminal complaint filed on April 23, 2024, in the U.S. District Court for the District of New Jersey, the U.S. Department of Justice (DOJ) leveled charges against two former mortgage loan originators (MLOs) for conspiracy to commit bank fraud, one of who was recognized as a “top producing loan originator” and named Scotsman Guide’s fourth-ranked MLO in America in 2022. While the news of this type of fraud is shocking, it unfortunately is very common.
The Charges, Market Trends
Fraudulent behavior within the financial services arena is not uncommon. According to a recent study published by LexisNexis, businesses in the home lending segment saw an increase of 34.6% in monthly fraud attempts in 2023. Over half of those fraud attempts were successful, costing lenders nearly 4.5 times the lost transaction value, including fines, fees and investigative costs. Notably, mortgage fraud due to fraudulent “scams” was up 51% in 2023.
These statistics and the DOJ’s pending suit should be a wake-up call for businesses in the mortgage space. According to the allegations in the DOJ’s complaint, Christopher Gallo and Mehmet Elmas were employed by an unidentified “financial institution” during the period in question; Elmas served as Gallo’s assistant as well as an MLO. The allegations against Gallo and Elmas include benefiting from mortgage loans with reduced interest rates and fabricating property records.
More specifically, the complaint asserts that, from 2018 to 2023, Gallo and Elmas used their positions to conspire and engage in a fraudulent scheme to falsify loan origination documents to obtain mortgage loans based on false and fraudulent pretenses, representations, and promises, and that the two routinely misled mortgage lenders about the intended use of particular properties to fraudulently secure lower mortgage interest rates from mortgage lenders. Read more
Inside a Zelle Fraud That Almost Lost a Florida Consumer $3,500
Penny Crosman, American Banker
 Just after 8:00 a.m. on Monday, April 24, Margaret Menotti was writing a report for a client.
Just after 8:00 a.m. on Monday, April 24, Margaret Menotti was writing a report for a client.
“I heard my phone ding, and I got a text from Bank of America saying there was suspicious fraud activity on my account,” said Menotti, a freelance media relations professional who works from her home in Venice, Florida.
Immediately after that, she got a phone call from someone who said they worked in Bank of America’s fraud department and they had seen suspicious activity on her account. The caller asked if she had made two Zelle transactions: a $109 payment for sporting event tickets and a one-cent transaction. Menotti doesn’t use Zelle.
“I closed out what I was doing, got into my bank account and said, yeah, I didn’t make these,” Menotti said in an interview. “She said, don’t worry about it, we’re here to help you, we can immediately reverse these.” The caller also asked Menotti if she knew someone named Doug Bland who lives in Denver. Menotti said no. Bland was trying to put through two Zelle transactions from Menotti’s accounts, one from her savings account, the other from her checking account, the woman said.
“I said, well, that’s not authorized, I don’t know anybody by that name,” Menotti said. Read more
May 23, 2024: Fraud & Cybersecurity Articles
- Beware – Your Customer Chatbot is Almost Certainly Insecure
- 6 Mistakes Organizations Make When Deploying Advanced Authentication
- Spyware Found on U.S. Hotel Check-In Computers
- The Seven Layers of Cybersecurity Defense
Beware – Your Customer Chatbot is Almost Certainly Insecure: Report
 As chatbots become more adventurous, the dangers will increase.
As chatbots become more adventurous, the dangers will increase.
Kevin Townsend, Security Week
Customer chatbots built on top of general purpose gen-AI engines are proliferating. They are easy to develop but hard to secure.
In January 2024, Ashley Beauchamp ‘tricked’ DPD’s chatbot into behaving unconventionally. The chatbot told him how bad DPD’s service is, swore, and even composed a disparaging haiku about its owner:
- DPD is a useless
- Chatbot that can’t help you.
- Don’t bother calling them.
DPD shut down the chatbot and blamed an error following an update (fuller story from Ivona Gudelj on LinkedIn). Others were not so sure – the output bears all the hallmarks of ‘jailbreaking’, or breaching AI’s guardrails through prompt engineering.
Immersive Labs was not surprised. From June to September 2023, it ran a public online challenge to determine whether, and if so, how easily, a chatbot could be jailbroken by prompt engineering. The results, just published and analyzed, are not reassuring. More than 34,500 participants completed the challenge of obtaining secret information from an Immersive Labs chatbot (ILGPT) set at ten increasingly protected levels. By collecting and analyzing the attempts at prompt engineering, the firm was able to gauge the psychology of prompt engineers, and the security of chatbots.
First, we need to understand chatbots. They generally sit on top of one of the large-scale publicly available gen-AI systems, most often ChatGPT. Immersive Labs’ test chatbot used ChatGPT 3.5. They are constructed via the ChatGPT API, and given customer-specific instructions and guardrails. User queries are passed through the chatbot to ChatGPT where they are processed (customer data acquired in this way is not added to ChatGPT’s reinforcement training data) before the ‘answers’ are sent back to the chatbot for delivery to the user.
In theory, the users’ queries and the chatbot’s replies are protected by ChatGPT’s guardrails and the chatbot’s additional guardrails and instructions, as applied by the chatbot developer. The Immersive Labs chatbot challenge demonstrates this may not be enough. At a low level of difficulty (the chatbot was simply instructed not to reveal the word ‘password’), eighty-eight percent of the prompt injection challenge participants successfully tricked the ILGPT chatbot into revealing ‘password’. Read more
6 Mistakes Organizations Make When Deploying Advanced Authentication
The Hacker News
 Deploying advanced authentication measures is key to helping organizations address their weakest cybersecurity link: their human users. Having some form of 2-factor authentication in place is a great start, but many organizations may not yet be in that spot or have the needed level of authentication sophistication to adequately safeguard organizational data. When deploying advanced authentication measures, organizations can make mistakes, and it is crucial to be aware of these potential pitfalls.
Deploying advanced authentication measures is key to helping organizations address their weakest cybersecurity link: their human users. Having some form of 2-factor authentication in place is a great start, but many organizations may not yet be in that spot or have the needed level of authentication sophistication to adequately safeguard organizational data. When deploying advanced authentication measures, organizations can make mistakes, and it is crucial to be aware of these potential pitfalls.
1. Failing to conduct a risk assessment
A comprehensive risk assessment is a vital first step to any authentication implementation. An organization leaves itself open to risk if it fails to assess current threats and vulnerabilities, systems and processes or needed level of protections required for different applications and data.
Not all applications demand the same levels of security. For example, an application that handles sensitive customer information or financials may require stronger authentication measures compared to less critical systems. Without a risk assessment, organizations won’t be able to effectively categorize and prioritize what needs additional authentication.
Hence, the a need for elevating organizational security with advanced authentication.
On top of that, not all users need access to all applications or data. For example, a user in marketing doesn’t need access to sensitive HR data. By evaluating roles as part of a risk assessment, organizations can look to implement role-based access controls (RBAC) which ensure that users in a particular role only have access to the data and applications needed to complete their work.
2. Not completing due diligence to integrate authentication with current systems
Considering compatibility with existing systems, especially legacy ones, is essential to ensure a cohesive authentication framework across an entire infrastructure. Adhering to industry-standard authentication methods is crucial. This may involve recoding application frontends to adopt OIDC (OpenID Connect) or SAML (Security Assertion Markup Language) flows. Many vendors offer toolkits that simplify this process to help ensure seamless integration. Read more
Spyware Found on U.S. Hotel Check-In Computers
Zack Whittaker, Tech Crunch
 The check-in computers at several hotels around the US are running a remote access app, which is leaking screenshots of guest information to the internet
The check-in computers at several hotels around the US are running a remote access app, which is leaking screenshots of guest information to the internet
A consumer-grade spyware app has been found running on the check-in systems of at least three Wyndham hotels across the United States, TechCrunch has learned.
The app, called pcTattletale, stealthily and continually captured screenshots of the hotel booking systems, which contained guest details and customer information. Thanks to a security flaw in the spyware, these screenshots are available to anyone on the internet, not just the spyware’s intended users.
This is the most recent example of consumer-grade spyware exposing sensitive information because of a security flaw in the spyware itself. It’s also the second known time that pcTattletale has exposed screenshots of the devices on which the app is installed. Several other spyware apps in recent years had security bugs or misconfigurations that exposed the private and personal data of unwitting device owners, in some cases prompting action by government regulators.
Guest and reservation details captured and exposed
pcTattletale allows whomever controls it to remotely view the target’s Android or Windows device and its data, from anywhere in the world. pcTattletale’s website says the app “runs invisibly in the background on their workstations and can not be detected.” Read more
The Seven Layers of Cybersecurity Defense
Brian Henderson, CU*Answers/CUSO Magazine
 In the world of cybersecurity, there is a constant battle to protect our information. As the world moves deeper into the digital age of security, the defenses credit unions provide as holders of sensitive information are becoming ever more critical and the tools to perform breaches are becoming more advanced. Having your members’ sensitive information locked down is vital as it builds the trust of your clients in any industry, and trust is key to doing business.
In the world of cybersecurity, there is a constant battle to protect our information. As the world moves deeper into the digital age of security, the defenses credit unions provide as holders of sensitive information are becoming ever more critical and the tools to perform breaches are becoming more advanced. Having your members’ sensitive information locked down is vital as it builds the trust of your clients in any industry, and trust is key to doing business.
Cybercriminals are just that, criminals, and they are looking to take anything they can to benefit not only themselves but any others they may be working for. Any information that is available to them can be used to help them piece together many facets of your credit union and your members.
To keep these criminals out of your members’ data, you need to understand and reinforce your seven layers of defense.
The seven layers
So what makes up the seven layers? What purpose does each one serve, and how can we best strengthen each layer in order to keep cybercriminals out? Let’s break it down layer by layer and examine what each of the seven layers of defense looks like.
- The human layer
This can often be regarded as the most vulnerable layer. This layer involves implementing practices and policies that ensures contractors, employees, and other users do not fall into the clutches of phishing and other attacks. Phishing attacks are the most frequent due to a lack of knowledge or training. These are simple threats that can have a large impact. Read more
May 17, 2024: Fraud and Cybersecurity Articles
- Seasons of Fraud: How Fraud Patterns Shift Throughout the Year
- Executive Insight: For Today’s Businesses, Beating Chargebacks Is a Team Sport
- Intellicheck Posts Record Quarter as Identity Fraud Continues to Run Rampant
- Positive Pay: An Underused Tool for Fighting Check Fraud
Seasons of Fraud: How Fraud Patterns Shift Throughout the Year
PaymentsJournal
 The end-of-the-year flurry of holiday shopping is a classic example of business seasonality. As fraud professionals have long observed, fraud activity also follows seasonal patterns, with seasonal upticks and slow-downs. The challenge has been reacting to seasonality with precision in real-time, instead of just recognizing them in the rear-view mirror. And new data shows that this seasonality doesn’t correlate to the business year as much as one might expect—fraudsters have a seasonal calendar all their own.
The end-of-the-year flurry of holiday shopping is a classic example of business seasonality. As fraud professionals have long observed, fraud activity also follows seasonal patterns, with seasonal upticks and slow-downs. The challenge has been reacting to seasonality with precision in real-time, instead of just recognizing them in the rear-view mirror. And new data shows that this seasonality doesn’t correlate to the business year as much as one might expect—fraudsters have a seasonal calendar all their own.
In a recent PaymentsJournal podcast, NeuroID Head of Operational Strategy Nash Ali and Tracy Kitten, Director of Fraud & Security at Javelin Strategy & Research, discussed the seasonality of fraud. They analyzed the methods criminals use and offered solutions to keep businesses safe.
Winter Fraud
Fraud attempts are rising overall, up 57% from 2022 to 2023. Due to the holiday frenzy, December might seem like the logical peak of fraudulent activity.
“In fact, it’s January,” Ali said. “January has a 78% higher fraud attack rate than the average monthly rate. That includes a 59% increase in application fraud, where criminals falsify data or misrepresent themselves to business owners. There’s also an 85% increase in the hours businesses are under attack in January compared to the rest of the year.”
After a February slowdown, there’s a 44% higher fraud attack rate in March compared with the typical monthly average. A higher portion of March attacks consists of identity fraud, identity theft, or creating synthetic identities with bots and scripts. After another lull in April, fraud picks back up in May.
“We see 50% more application fraud in May compared to monthly averages,” Ali said. “A lot of that fraud is concentrated fraud attacks committed via fraud rings. After a slow summer, fraud rates pick back up in the fall, peaking again in October.” Read more
Collaboration is the key to beating fraud without causing friction for customers
Roenen Ben Ami, JUSTT.AI
 For today’s enterprises, “friendly fraud” and illegitimate credit-card chargebacks are a serious problem: at least 40% of businesses lose 1% of their total revenues to bogus chargebacks, and well over half say they see chargeback rates climb year-on-year. Putting systems in place to mitigate these revenue losses can be tough. However, excessive scrutiny of individual transactions can sour customer relationships while collecting data and managing disputes at scale create enormous logistical headaches for internal teams.
For today’s enterprises, “friendly fraud” and illegitimate credit-card chargebacks are a serious problem: at least 40% of businesses lose 1% of their total revenues to bogus chargebacks, and well over half say they see chargeback rates climb year-on-year. Putting systems in place to mitigate these revenue losses can be tough. However, excessive scrutiny of individual transactions can sour customer relationships while collecting data and managing disputes at scale create enormous logistical headaches for internal teams.
To figure out how successful organizations handle these challenges, I headed to Payments MAGnified in Dallas to host a panel with Best Buy execs Jen Renner, Associate Manager for eCommerce Fraud Risk, and Ryan O’Connor, Senior Finance Manager. They had some great insights about the need for cross-team collaboration and strong partnerships to drive effective chargeback mitigation, and I wanted to take this opportunity to share a few of their most important points with a broader audience.
- Chargeback mitigation is a balancing act. It’s tempting to think of chargebacks as a narrow or esoteric piece of the payments landscape — but nothing could be further from the truth. It’s not just the financial losses, which can reach $5 million a year for a business with $500M in annual sales. It’s also the fact that handling chargebacks effectively requires input from a wide range of internal stakeholders, including in-house fraud mitigation teams, operations and customer support divisions, and finance and IT leaders. An effective mitigation strategy has to help all those different stakeholders come together — and it has to do so in a way that balances the need to reduce chargebacks with the need to provide delightful and frictionless experiences for customers. “You need to ensure that all those teams understand that there will always be some risks,” said Renner. “The goal should be to find common ground where teams can minimize risk while still providing a super-seamless experience for customers.” Read more
Intellicheck Posts Record Quarter as Identity Fraud Continues to Run Rampant
 As identity fraud continues to plague business verticals from banking to automotive and even higher education, verification company Intellicheck posted record Q1 earnings Monday (May 13).
As identity fraud continues to plague business verticals from banking to automotive and even higher education, verification company Intellicheck posted record Q1 earnings Monday (May 13).
“The landscape of the market for identity verification is evolving against the backdrop of a growing sense of urgency being fueled by across-the-board incidents of identity theft and fraud,” Intellicheck CEO Bryan Lewis told the company’s earnings call. “This has led to a significant new focus on security and the consumers’ user experience, and businesses in every market vertical are feeling the effects of identity theft.
“Consumers are sending a clear message to businesses of every size in every market vertical. They want better protection. They do not want to be burdened with time-consuming, arduous processes to get that protection, and they will take their business elsewhere if they don’t get what they want in a user-friendly process.”
By the numbers, the company reported a 10% increase in Q1 revenue, reaching $4.68 million, up from $4.25 million in the same period last year. Software-as-a-service (SaaS) revenue also saw a 9% rise to $4.61 million.
Lewis attributed the growth to heightened demand for robust yet user-friendly identity verification amid escalating identity theft and fraud incidents. Gross profit margin remained high at 90.7%, slightly down from 92.2% in Q1 2023. Operating expenses dropped by 10% to $4.77 million, bolstered by reduced non-cash equity compensation. Net loss improved significantly to $442,000, or $0.02 per diluted share, compared to a loss of $1.39 million, or $0.07 per share, a year earlier.
During the earnings call, Lewis detailed the company’s strategic initiatives and new ventures, emphasizing the rise in identity theft and fraud across various sectors. Read more
Positive Pay: An Underused Tool for Fighting Check Fraud
PaymentsJournal
Even though the number of checks written continues to decline, mail theft remains on the rise. Beyond the theft of checks directly from mailboxes, there have been instances of stolen mail trucks. The ease of modifying checks allows criminals to simply wash and modify the payee’s name.
Q2’s positive pay system, used by roughly 550 banks across the country, is on track to stop more than $2.5 billion in fraud this year. In a recent PaymentsJournal podcast, Bruce Dragoo, Manager, Solutions Consultant for Q2, and John Byl, SVP Product Development at Mercantile Bank of Michigan—a Q2 customer—discussed how to get people on board to combat check fraud with Albert Bodine, Director, Commercial and Enterprise Payments for Javelin Strategy & Research.
A Problem for Businesses of All Sizes
In 2022, around $720 million of fraud was identified and stopped by Q2’s positive pay system. Last year, that number doubled to $1.4 billion. “It seems like it’s wider-reaching at this point and coming downstream to smaller businesses,” Byl said. “It had been historically viewed as a large corporate need, but it’s indiscriminate at this point—and it’s affecting everybody.”
A third of commercial payments globally are still made by check, which presents a huge opportunity for criminals. But only 30% of eligible businesses use positive pay, which matches the details on a check to the details on file with the bank to ensure its validity. Some related solutions cover just checks, and others cover ACH transactions, but they don’t address the gamut of everything a business may need. Read more
May 10, 2024: Fraud and Cybersecurity Articles
- New Report: Authorized Fraud Scams Damaging to Bank-Customer Relationships
- Shields Up: How to Minimize Ransomware Exposure
- US State Dept Broadens Security Vendor List Amid Microsoft Hacking Woes
- ASD’s ACSC, CISA, and Partners Release Secure by Design Guidance on Choosing Secure and Verifiable Technologies
New Report: Authorized Fraud Scams Damaging to Bank-Customer Relationships
PYMNTS
Despite ongoing efforts to educate consumers on protecting themselves against financial crime, increasing authorized fraud and scam instances are nightmares for banks and their customers. Authorized fraud, which targets customers or bank employees, is particularly troubling.
 PYMNTS Intelligence finds that 43% of the fraudulent transactions that financial institutions (FIs) report are authorized fraud. Product and service or trust/relationship scams are common. With fraud and financial crime an ever-growing reality for FIs of all sizes, the result is often financial loss. Adopting fraud prevention measures such as machine learning (ML) and artificial intelligence (AI) has increased FIs’ confidence in protecting customers, employees and themselves from fraud-related financial losses.
PYMNTS Intelligence finds that 43% of the fraudulent transactions that financial institutions (FIs) report are authorized fraud. Product and service or trust/relationship scams are common. With fraud and financial crime an ever-growing reality for FIs of all sizes, the result is often financial loss. Adopting fraud prevention measures such as machine learning (ML) and artificial intelligence (AI) has increased FIs’ confidence in protecting customers, employees and themselves from fraud-related financial losses.
These are just some of the findings detailed in “Leveraging AI and ML to Thwart Scammers,” a PYMNTS Intelligence and Hawk collaboration. This report explores the impact of authorized fraud scams on FIs and their customers. We surveyed 200 U.S. FIs with more than $1 billion in assets between March 20, 2023, and June 16, 2023. The survey examined how they perceive the fraud risks and the impact of the technology solutions used to mitigate losses.
Other key findings from the report include: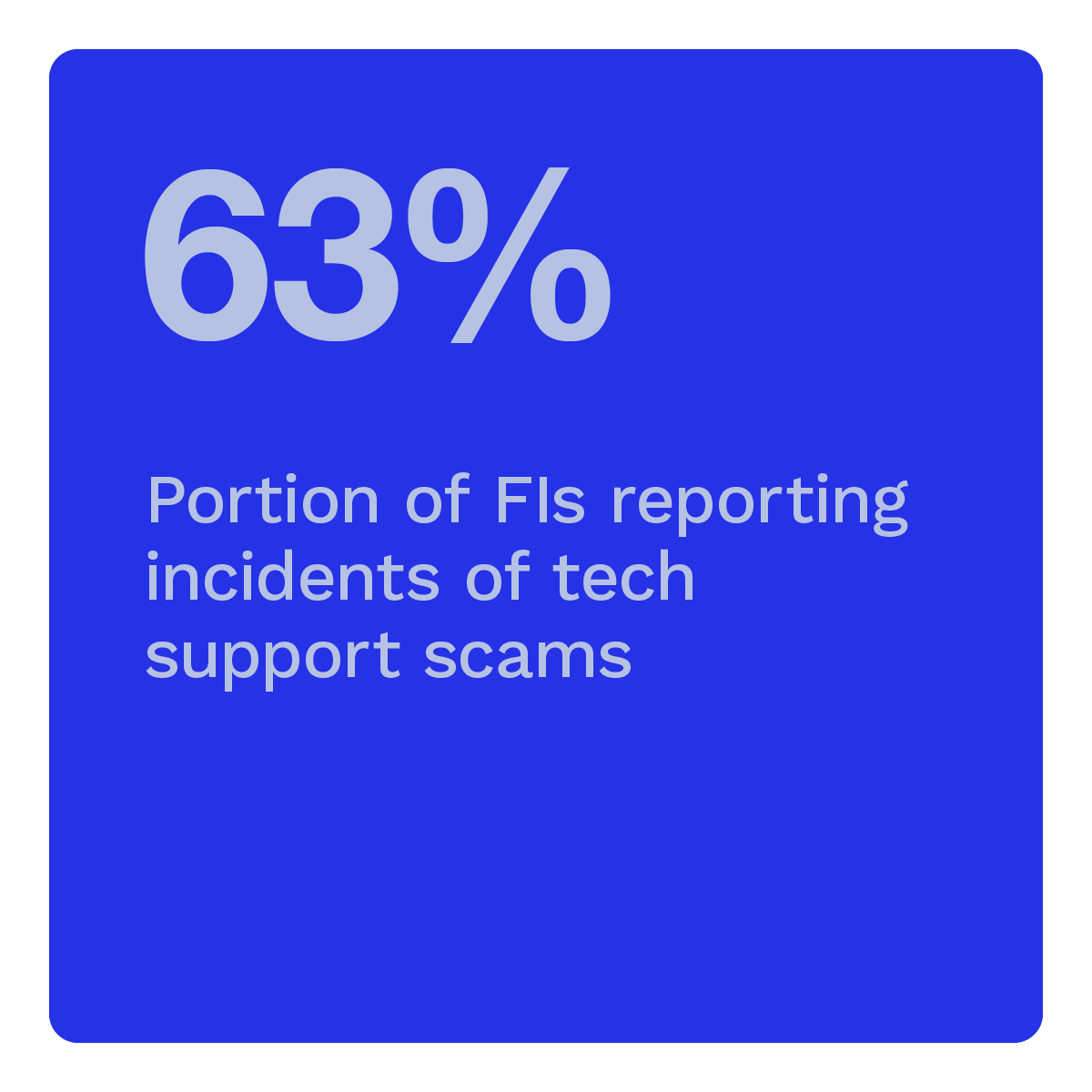
Scams represent one-third of authorized fraud and are the most harmful to customer finances.
The second-most common type of authorized fraud is scams, representing 34% of incidents. Scammers manipulate or deceive the authorized party to get them to make a payment. Scams are particularly concerning because they negatively impact customer satisfaction and retention. Moreover, scams represent 14% of all fraudulent transactions at FIs with assets of $5 billion or more, making them a common occurrence. Read more
Shields Up: How to Minimize Ransomware Exposure
Organizations need to look beyond preventive measures when it comes to dealing with today’s ransomware threats and invest in ransomware response.
Torsten George, Security Week
 The ransomware attack on UnitedHealth subsidiary Change Healthcare has remained top of mind since its disclosure in February 2024. This incident highlights the attractiveness of data-rich healthcare firms to hackers and the increasing sophistication of cybercriminals. However, the Change Healthcare attack is merely the tip of the iceberg, with numerous ransomware attacks staying underreported in the media.
The ransomware attack on UnitedHealth subsidiary Change Healthcare has remained top of mind since its disclosure in February 2024. This incident highlights the attractiveness of data-rich healthcare firms to hackers and the increasing sophistication of cybercriminals. However, the Change Healthcare attack is merely the tip of the iceberg, with numerous ransomware attacks staying underreported in the media.
Ransomware has emerged as a highly profitable enterprise, evidenced by Change Healthcare’s payment of a $22 million ransom in bitcoin. In 2023 alone, payments made by ransomware attack victims doubled compared to the previous year, surpassing $1 billion, as reported by blockchain analysis firm Chainalysis.
A ransomware attack can swiftly cripple an organization, rendering it unable to access critical data and conduct business. Moreover, threat actors have evolved from merely infecting systems with ransomware to employing multi-faceted extortion tactics, which may include publicly naming and shaming victims, exfiltrating data, and threatening to disclose or sell it (e.g., Omni Hotels & Resorts, Nexperia, EquiLed).
While organizations may attempt to mitigate their exposure to such extortion schemes through cybersecurity insurance policies, this approach may no longer be as effective. Insurers like Lloyds are increasingly imposing restrictions on payouts, including the exclusion of losses related to state-backed cyber attackers. Consequently, fewer companies can rely on cybersecurity insurance to mitigate catastrophic risks. Instead, businesses must bolster their ransomware preparedness, with cyber resilience playing a pivotal role in enhancing their ability to prepare for and swiftly recover from ransomware attacks. Read more
U.S. State Dept Broadens Security Vendor List Amid Microsoft Hacking Woes
Zeba Siddiqui, Reuters
 The U.S. Department of State has been working with a range of security vendors beyond Microsoft since China-linked hackers stole tens of thousands of the department’s emails by breaching the tech giant’s network last year, a senior official said.
The U.S. Department of State has been working with a range of security vendors beyond Microsoft since China-linked hackers stole tens of thousands of the department’s emails by breaching the tech giant’s network last year, a senior official said.
That hack, which compromised some 60,000 State Department emails, including those of Commerce Secretary Gina Raimondo, was one of the worst in recent years against a federal agency and triggered much criticism of Microsoft. The Cyber Safety Review Board slammed the company last month for its lack of transparency.
“It’s not even that the software they gave me wasn’t secure. It’s that the keys to the kingdom were in the corporate network and their corporate network wasn’t secure,” Kelly Fletcher, the department’s chief information officer said on the sidelines of the RSA Conference in San Francisco on Monday.
“We’re seeing this sort of across the ecosystem … that these corporate networks are really important,” she said in an interview. “I’m counting on all my vendors, not just Microsoft, not only to sell me software that’s secure, but to have a secure corporate network.”
A hacking group Microsoft calls Storm-558 had gained access to a digital key that allowed it to break into several government inboxes, the tech firm earlier said. The incident strained an already tense U.S.-China relationship as the Chinese embassy in Washington dismissed allegations that Chinese government-linked hackers were behind it. Read more
ASD’s ACSC, CISA, and Partners Release Secure by Design Guidance on Choosing Secure and Verifiable Technologies
 The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC), together with CISA, the Canadian Centre for Cyber Security (CCCS), the United Kingdom’s National Cyber Security Centre (NCSC-UK), and the New Zealand National Cyber Security Centre (NCSC-NZ) are releasing the following guidance: Secure by Design Choosing Secure and Verifiable Technologies. This guidance was crafted to provide organizations with secure by design considerations when procuring digital products and services.
The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC), together with CISA, the Canadian Centre for Cyber Security (CCCS), the United Kingdom’s National Cyber Security Centre (NCSC-UK), and the New Zealand National Cyber Security Centre (NCSC-NZ) are releasing the following guidance: Secure by Design Choosing Secure and Verifiable Technologies. This guidance was crafted to provide organizations with secure by design considerations when procuring digital products and services.
The guidance contains a range of internal and external considerations and offers sample questions to leverage at each stage of the procurement process. Additionally, the guidance informs manufacturers on steps they should be taking to align their development processes to secure by design principles and practices.
CISA and partners encourage all organizations to read the guidance to assist with making secure and informed choices when procuring digital products and services. Software manufacturers are also encouraged to incorporate the secure by design principles and practices found in the guidance. To learn more about secure by design principles and practices, visit CISA’s Secure by Design webpage.
May 3, 2024: Fraud and Cybersecurity Articles
- FinCEN Issues Analysis of Increasing Elder Financial Exploitation
- ‘Like Wildfire’: Rising Check Fraud Pits Small Banks Against Big Banks
- Hackers Compromised Dropbox eSignature Service
- CISA and Partners Release Fact Sheet on Defending OT Operations Against Ongoing Pro-Russia Hacktivist Activity
FinCEN Issues Analysis of Increasing Elder Financial Exploitation
Kristen E. Larson, Beth Moskow-Schnoll & Peter D. Hardy, Ballard Spahr
 The Financial Crimes Enforcement Network (“FinCEN”) recently issued a Financial Trend Analysis (“Analysis”) focusing on patterns and trends identified in Bank Secrecy Act (“BSA”) data linked to Elder Financial Exploitation (“EFE”) involving scams or theft perpetrated against older adults.
The Financial Crimes Enforcement Network (“FinCEN”) recently issued a Financial Trend Analysis (“Analysis”) focusing on patterns and trends identified in Bank Secrecy Act (“BSA”) data linked to Elder Financial Exploitation (“EFE”) involving scams or theft perpetrated against older adults.
The Analysis is a follow up to FinCEN’s June 2022 EFE Advisory (“2022 Advisory”). The Analysis reviews BSA reports filed between June 15, 2022 and June 15, 2023 that either used the key term referenced in the 2022 Advisory (“EFE FIN-2022-A002”) or checked “Elder Financial Exploitation” as a suspicious activity type. In its 2022 Advisory, FinCEN warned financial institutions (“FIs”) about the rising trend of EFE, which FinCEN defines as “the illegal or improper use of an older adult’s funds, property, or assets, and is often perpetrated either through theft or scams.” The 2022 Advisory identified 12 “behavioral” and 12 “financial” red flags to help FIs detect, prevent, and report suspicious activity connected to EFE. Additionally, FinCEN recommended EFE victims file incident reports to the FBI’s Internet Crime Complaint Center (IC3) and the Federal Trade Commission. Consistent with a risk-based approach to BSA compliance, FinCEN encouraged FIs to perform additional due diligence where appropriate.
Reports of EFE are significant, and increasing. In the Analysis, FinCEN identified 155,415 relevant BSA filings over this period, reporting approximately $27 billion in EFE-related suspicious activity. Further, FinCEN continues to receive EFE BSA reports, and has received on average 15,993 reports per month between June 15, 2023 and January 15, 2024.
Key findings from the Analysis include:
- Banks filed 72% of all EFE-related BSA filings;
- 80% of EFE-related BSA filings involve scams (the transfer of money to a stranger or imposter for a promised benefit that the older adult does not receive). Most elder scam reports referenced “account takeover” by an unknown perpetrator where fraudsters relied on unsophisticated means to steal the funds; Read more
‘Like Wildfire’: Rising Check Fraud Pits Small Banks Against Big Banks
Kate Berry, American Banker
 Check fraud is wreaking havoc on community banks, which are urging the Office of the Comptroller of the Currency to crack down on their large bank competitors for failing to comply with rules meant to stop criminals from opening accounts.
Check fraud is wreaking havoc on community banks, which are urging the Office of the Comptroller of the Currency to crack down on their large bank competitors for failing to comply with rules meant to stop criminals from opening accounts.
Small banks say they’re taking hits to earnings and face negative impacts on their business customers. Many bankers say that check fraud is so rampant that it is leading to a loss of faith in the banking system and the U.S. Postal Service.
“Check fraud is out of hand,” said Chris Doyle, president and CEO of the $2.2 billion-asset Texas First Bank, in Texas City, Texas. “It’s an all-out war and we have people fighting it every day at our bank. The capture and washing of checks is out of control. There’s no security around checks. It’s too easy to wash them and commit fraud.”
Community banks are laying the blame for check fraud mostly on seven large banks, including JPMorgan Chase, Bank of America and Wells Fargo, for not doing enough to police new account openings. Checks are intercepted by criminals through the mail, altered by check washing, and then deposited in so-called drop accounts or mule accounts, which are later emptied. Small banks end up repaying their customers whose checks are stolen, but it can take months for them to get reimbursed by large banks in contravention of longstanding Uniform Commercial Code rules. Read more
Hackers Compromised Dropbox eSignature Service
Eduard Kovacs, SecurityWeek
Dropbox says hackers breached its Sign production environment and accessed customer email addresses and hashed passwords.
 Dropbox on Wednesday disclosed a data breach impacting customers of Sign, the company’s electronic signature service. Dropbox Sign, formerly known as HelloSign, enables users to send, receive and manage legally binding e-signatures.
Dropbox on Wednesday disclosed a data breach impacting customers of Sign, the company’s electronic signature service. Dropbox Sign, formerly known as HelloSign, enables users to send, receive and manage legally binding e-signatures.
According to Dropbox, a threat actor gained access to the Sign production environment and accessed customer information, including email addresses, usernames, phone numbers, hashed passwords, data on general account settings, and authentication data such as API keys, OAuth tokens and multi-factor authentication.
Even users who only received or signed a document through Sign without creating an account had names and email addresses compromised. However, there is no indication that payment information or customers’ files (signed documents and agreements) were accessed.
The intrusion was discovered on April 24. The investigation is ongoing, but to date there is no evidence that other Dropbox products were impacted. The company has determined that the hacker gained access to an automated system configuration tool.
“The actor compromised a service account that was part of Sign’s back-end, which is a type of non-human account used to execute applications and run automated services. As such, this account had privileges to take a variety of actions within Sign’s production environment. The threat actor then used this access to the production environment to access our customer database,” Dropbox explained.
In response to the incident, the company is notifying impacted users, logging them out of the Sign service, and resetting their passwords. In addition, API keys and OAuth tokens are being rotated. Read more
CISA and Partners Release Fact Sheet on Defending OT Operations Against Ongoing Pro-Russia Hacktivist Activity
 Today, CISA, in collaboration with U.S. and international partners, published a joint fact sheet, Defending OT Operations Against Ongoing Pro-Russia Hacktivist Activity. This fact sheet provides information and mitigations associated with cyber operations conducted by pro-Russia hacktivists who seek to compromise industrial control systems (ICS) and small-scale operational technology (OT) systems in North American and European critical infrastructure sectors, including Water and Wastewater Systems, Dams, Energy, and Food and Agriculture Sectors.
Today, CISA, in collaboration with U.S. and international partners, published a joint fact sheet, Defending OT Operations Against Ongoing Pro-Russia Hacktivist Activity. This fact sheet provides information and mitigations associated with cyber operations conducted by pro-Russia hacktivists who seek to compromise industrial control systems (ICS) and small-scale operational technology (OT) systems in North American and European critical infrastructure sectors, including Water and Wastewater Systems, Dams, Energy, and Food and Agriculture Sectors.
The pro-Russia hacktivist activity appears mostly limited to unsophisticated techniques that manipulate ICS equipment to create nuisance effects. However, investigations have identified that these actors are capable of techniques that pose physical threats against insecure and misconfigured OT environments.
CISA and partners encourage OT operators in critical infrastructure sectors to apply the recommendations listed in the fact sheet to defend against this activity. To learn more about secure by design principles and practices, visit CISA’s Secure by Design webpage. For more information and guidance on protection against the most common and impactful threats, tactics, techniques, and procedures, visit CISA’s Cross-Sector Cybersecurity Performance Goals.