 The National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Cybersecurity and Infrastructure Security Agency (CISA) released a Cybersecurity Information Sheet (CSI), Contextualizing Deepfake Threats to Organizations, which provides an overview of synthetic media threats, techniques, and trends. Threats from synthetic media, such as deepfakes, have exponentially increased—presenting a growing challenge for users of modern technology and communications, including the National Security Systems (NSS), the Department of Defense (DoD), the Defense Industrial Base (DIB), and national critical infrastructure owners and operators. Between 2021 and 2022, U.S. Government agencies collaborated to establish a set of employable best practices to take in preparation and response to the growing threat. Public concern around synthetic media includes disinformation operations, designed to influence the public and spread false information about political, social, military, or economic issues to cause confusion, unrest, and uncertainty.
The National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Cybersecurity and Infrastructure Security Agency (CISA) released a Cybersecurity Information Sheet (CSI), Contextualizing Deepfake Threats to Organizations, which provides an overview of synthetic media threats, techniques, and trends. Threats from synthetic media, such as deepfakes, have exponentially increased—presenting a growing challenge for users of modern technology and communications, including the National Security Systems (NSS), the Department of Defense (DoD), the Defense Industrial Base (DIB), and national critical infrastructure owners and operators. Between 2021 and 2022, U.S. Government agencies collaborated to establish a set of employable best practices to take in preparation and response to the growing threat. Public concern around synthetic media includes disinformation operations, designed to influence the public and spread false information about political, social, military, or economic issues to cause confusion, unrest, and uncertainty.
The authoring agencies urge organizations review the CSI for recommended steps and best practices to prepare, identify, defend against, and respond to deepfake threats.
To report suspicious activity or possible incidents involving deepfakes, contact one of the following agencies:
- Cybersecurity Report Feedback: [email protected]
- Internet Crime Complaint Center (IC3) at IC3.gov or contact a local FBI field office
- CISA’s Incident Reporting System or through the agency’s 24/7 Operations Center at [email protected] or (888) 282-0870
October 05, 2022 — The Federal Bureau of Investigation (FBI) and CISA have published a joint public service announcement that:
- Assesses malicious cyber activity aiming to compromise election infrastructure is unlikely to result in large-scale disruptions or prevent voting.
- Confirms “the FBI and CISA have no reporting to suggest cyber activity has ever prevented a registered voter from casting a ballot, compromised the integrity of any ballots cast, or affected the accuracy of voter registration information.”
The PSA also describes the extensive safeguards in place to protect election infrastructure and includes recommendations for protecting against election-related cyber threats.
Malicious Cyber Activity Against Election Infrastructure Unlikely to Disrupt or Prevent Voting
 The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) assess that any attempts by cyber actors to compromise election infrastructure are unlikely to result in large- scale disruptions or prevent voting. As of the date of this report, the FBI and CISA have no reporting to suggest cyber activity has ever prevented a registered voter from casting a ballot, compromised the integrity of any ballots cast, or affected the accuracy of voter registration information. Any attempts tracked by FBI and CISA have remained localized and were blocked or successfully mitigated with minimal or no disruption to election processes.
The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) assess that any attempts by cyber actors to compromise election infrastructure are unlikely to result in large- scale disruptions or prevent voting. As of the date of this report, the FBI and CISA have no reporting to suggest cyber activity has ever prevented a registered voter from casting a ballot, compromised the integrity of any ballots cast, or affected the accuracy of voter registration information. Any attempts tracked by FBI and CISA have remained localized and were blocked or successfully mitigated with minimal or no disruption to election processes.
 The public should be aware that election officials use a variety of technological, physical, and procedural controls to mitigate the likelihood of malicious cyber activity (e.g., phishing, ransomware, denial of service, or domain spoofing) affecting the confidentiality, integrity, or availability of election infrastructure systems or data that would alter votes or otherwise disrupt or prevent voting. These include failsafe measures, such as provisional ballots and backup pollbooks, and safeguards that protect against voting malfunctions (e.g., logic and accuracy testing, chain of custody procedures, paper ballots, and post-election audits). Given the extensive safeguards in place and distributed nature of election infrastructure, the FBI and CISA continue to assess that attempts to manipulate votes at scale would be difficult to conduct undetected.
The public should be aware that election officials use a variety of technological, physical, and procedural controls to mitigate the likelihood of malicious cyber activity (e.g., phishing, ransomware, denial of service, or domain spoofing) affecting the confidentiality, integrity, or availability of election infrastructure systems or data that would alter votes or otherwise disrupt or prevent voting. These include failsafe measures, such as provisional ballots and backup pollbooks, and safeguards that protect against voting malfunctions (e.g., logic and accuracy testing, chain of custody procedures, paper ballots, and post-election audits). Given the extensive safeguards in place and distributed nature of election infrastructure, the FBI and CISA continue to assess that attempts to manipulate votes at scale would be difficult to conduct undetected.
Election systems that house voter registration information or manage non- voting election processes continue to be a target of interest for malicious threat actors. Cyber actors may also seek to spread or amplify false or exaggerated claims of cybersecurity compromises to election infrastructure; however, these attempts would not prevent voting or the accurate reporting of results.a
The FBI and CISA will continue to quickly respond to any potential threats, provide recommendations to harden election infrastructure, notify stakeholders of threats and intrusion activity, and impose risks and consequences on cyber actors seeking to threaten U.S. elections.
Recommendations
- For information about registering to vote, polling locations, voting by mail, provisional ballot process, and final election results, rely on state and local government election officials.
- Remain alert to election-related schemes which may attempt to impede election administration.
- Be wary of emails or phone calls from unfamiliar email addresses or phone numbers that make suspicious claims about the elections process or of social media posts that appear to spread inconsistent information about election-related incidents or results.
- Do not communicate with unsolicited email senders, open attachments from unknown individuals, or provide personal information via email without confirming the requester’s identity. Be aware that many emails requesting your personal information often appear to be legitimate.
- Verify through multiple, reliable sources any reports about compromises of voter information or voting systems, and consider searching for other reliable sources before sharing such information via social media or other avenues.
- Be cautious with websites not affiliated with local or state government that solicit voting information, like voter registration information. Websites that end in “.gov” or websites you know are affiliated with your state or local election office are usually trustworthy. Be sure to know what your state and local elections office websites are in advance to avoid inadvertently providing your information to nefarious websites or actors.
- Report potential crimes—such as cyber targeting of voting systems—to your local FBI Field Office.
- Report cyber-related incidents on election infrastructure to your local election officials and CISA ([email protected]).
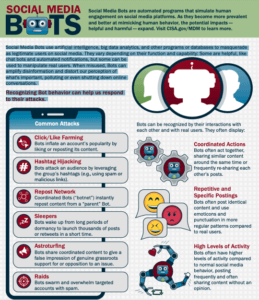 Last week the Cybersecurity and Infrastructure Security Agency published a quick guide on ID-ing Social Media Bots; automated programs that simulate human engagement on social media platforms.
Last week the Cybersecurity and Infrastructure Security Agency published a quick guide on ID-ing Social Media Bots; automated programs that simulate human engagement on social media platforms.
Social Media Bots use artificial intelligence, big data analytics, and other programs or databases to masquerade
as legitimate users on social media. They vary depending on their function and capability: Some are helpful, like
chat bots and automated notifications, but some can be used to manipulate real users. When misused, Bots can
amplify disinformation and distort our perception of what’s important, polluting or even shutting down online
conversations.
Recognizing Bot behavior can help us respond to their attacks.
(Nov. 5, 2021) Addressing and mitigating actively exploited vulnerabilities on all federal agency computer networks is the aim of a directive issued this week by the federal agency that oversees cybersecurity, which the agency said is a first-ever federal government-wide requirement.
In issuing the order, the Cybersecurity and Infrastructure Security Agency (CISA) said it also encourages state and local governments, as well as the private sector, to also take action.
The “Binding Operational Directive” (BOD 22-01), CISA said, is sending a “clear message to all organizations across the country to focus patching on the subset of vulnerabilities that are causing harm now, and enable CISA to drive continuous prioritization of vulnerabilities based on our understanding of adversary activity.”
The order, the agency said, applies to all software and hardware found on federal information systems, including those managed on agency premises or hosted by third parties on an agency’s behalf. According to agency Director Jen Easterly, the order lays out clear requirements for federal civilian agencies to take immediate action to improve their vulnerability management practices and dramatically reduce their exposure to cyber attacks.
“While this Directive applies to federal civilian agencies, we know that organizations across the country, including critical infrastructure entities, are targeted using these same vulnerabilities,” she said. “It is therefore critical that every organization adopt this Directive and prioritize mitigation of vulnerabilities listed in CISA’s public catalog.”
The agency noted that the order prioritizes resources for patching vulnerabilities that are most likely to result in a damaging intrusion into federal agencies and American businesses, “building upon existing methods widely used to prioritize vulnerabilities by many organizations today.”
LINK:
CISA Releases Directive on Reducing The Significant Risk Of Known Exploited Vulnerabilities
(May 14, 2021) If you were one of the unfortunate but countless number of folks sitting in line at the gas pumps this week – wondering “what can I do to stop this?” – consider the NASCUS Cybersecurity eSchool (in partnership with CUNA) set for Sept. 3 to Nov. 9.
The hacking and ransomware attack on the Colonial Pipeline – which disrupted gasoline delivery to stations up and down the East Coast, leading to panic buying and long lines – has underscored the need for cybersecurity preparation and protection, according to many experts.
Aimed at anyone at credit unions and regulators needing cybersecurity training, the Cybersecurity eSchool multi-week program includes sessions on: anatomy of a ransomware attack; cybersecurity strategy, developing and strengthening an information security policy; building staff and board awareness; threat hunting; security frameworks and more.
For more information, including the agenda and registration, see the link below.
Also: This week NCUA and the Cybersecurity and Infrastructure Agency (CISA) scheduled a May 26 one-hour webinar (at 2 p.m.), for credit unions on preventing and addressing cyberattacks. NCUA said the session will focus on (among other things) Identifying risks to products, services, and assets and monitoring the security of networks.
LINKS:
NASCUS Cybersecurity eSchool, in Partnership with CUNA
Registration Now Open for NCUA, CISA Cybersecurity Webinar
(March 5, 2021) NCUA’s Rodney Hood was named the agency’s representative on the board of NeighborWorks America, a public-private organization that promotes affordable housing and community development, NCUA Chairman Todd Harper said this week. The group’s board consists of representatives of financial regulatory agencies and the U.S. Department of Housing and Urban Development (HUD) and includes (in addition to Hood): Martin Gruenberg, member of the FDIC Board, serving as NeighborWorks’ board chair; Michelle W. Bowman, member of the Federal Reserve Board of Governors, serving as vice chair; Grovetta Gardineer, senior deputy comptroller for bank supervision policy at the (OCC) … Federal civilian agencies were advised this week to install a patch for Microsoft Exchange for on-premises products – or disconnect those products until they do update with the patch. The “emergency directive” issued by the federal Cybersecurity and Infrastructure Security Agency (CISA) said the directive was issued in response to observed active exploitation of these products using previously unknown vulnerabilities. The directive also requires agencies to collect forensic images (if they are currently able to do so), and requires agencies to search for known indicators of compromise after patching; if indicators are found, they agencies are advised, they should contact CISA to begin incident response activities … The State of Washington, Dept. of Financial Institutions, is inviting applications for the position of program manager, chief of specialty examinations; see the NASCUS “state job opportunities” page (link below) for more details … NASCUS now has its own Facebook page, an effort undertaken by NASCUS Senior Director of Communications and Marketing Amanda Tuckey to expand the association’s reach. “We’re welcoming everyone to follow our page for daily NASCUS/industry news,” Tuckey said.
LINKS:
Chairman Harper Appoints Hood to NeighborWorks America Board of Directors
CISA issues emergency directive requiring federal agencies to patch critical vulnerability
NASCUS state job opportunities (WA program manager, chief of specialty exams)