
Financial Crimes Enforcement Network (FinCEN), Treasury
ACTION: Advance notice of proposed rulemaking. No-Action Letter Process
TOPIC: FinCEN is issuing this advance notice of proposed rulemaking (ANPRM) to solicit public comment on questions relating to the implementation of a no-action letter process at FinCEN. Given that the addition of a no-action letter process at FinCEN may affect or overlap with other forms of regulatory guidance and relief that FinCEN already offers, including administrative rulings and exceptive or exemptive relief, this ANPRM, among other things, seeks public input on whether a no-action letter process should be implemented and, if so, how the no-action letter process should interact with those other forms of relief.
DATES: Comments must be received by August 5, 2022.
Click here to read the full NASCUS Summary (Member login required.)
 BUREAU OF CONSUMER FINANCIAL PROTECTION ( 12 CFR Part 1006) Debt Collection Practices (Regulation F); Pay-to-Pay Fees
BUREAU OF CONSUMER FINANCIAL PROTECTION ( 12 CFR Part 1006) Debt Collection Practices (Regulation F); Pay-to-Pay Fees
ACTION: Advisory opinion
TOPIC: Section 808(1) of the Fair Debt Collection Practices Act (FDCPA or Act) prohibits debt collectors from collecting any amount (including any interest, fee, charge, or expense incidental to the principal obligation) unless that amount is expressly authorized by the agreement creating
the debt or permitted by law. The Consumer Financial Protection Bureau (CFPB) issues this advisory opinion to affirm that this provision prohibits debt collectors from collecting pay-to-pay or ‘‘convenience’’ fees, such as fees imposed for making a payment online or by phone, when those fees are not expressly authorized by the agreement creating the debt or expressly authorized by law. This advisory opinion also clarifies that a debt collector may also violate section 808(1) when the debt collector collects pay-topay fees through a third-party payment processor.
DATES: This advisory opinion is effective on July 5, 2022.
Click here to read the full NASCUS Summary (Member login required.)
 BUREAU OF CONSUMER FINANCIAL PROTECTION
BUREAU OF CONSUMER FINANCIAL PROTECTION
ACTION: Request for Information Regarding Employer-Driven Debt
TOPIC: The Consumer Financial Protection Bureau (CFPB or Bureau) is charged with monitoring markets for consumer financial products and services to ensure that they are fair, transparent, and competitive. As part of this mandate, the CFPB is seeking input from the public on debt obligations incurred by consumers in the context of an employment or independent contractor arrangement. Areas of inquiry include prevalence, pricing and other terms of the obligations, disclosures, dispute resolution, and the servicing and collection of these debts.
DATES: Comments must be received by September 7, 2022.
Click here to read the full NASCUS Summary (Member login required.)
 BUREAU OF CONSUMER FINANCIAL PROTECTION
BUREAU OF CONSUMER FINANCIAL PROTECTION
ACTION: Advance notice of proposed rulemaking. Credit Card Late Fees and Late Payments
TOPIC: In order to support its rulemaking and other functions, the Consumer Financial Protection Bureau (Bureau or CFPB) is charged with monitoring for risks to consumers in the offering or provision of consumer financial products or services, including developments in markets for such products or services. As part of this mandate, the Bureau is seeking information from credit card issuers, consumer groups, and the public regarding credit card late fees and late payments, and card issuers’ revenue and expenses. For example, the Bureau is seeking information relevant to certain provisions related to credit card late fees in the Credit Card Accountability Responsibility and Disclosure Act of 2009 (CARD Act or the Act) and Regulation Z. Areas of inquiry include: factors used by card issuers to set late fee amounts; card issuers’ costs and losses associated with late payments; the deterrent effects of late fees; cardholders’ late payment behavior; methods that card issuers use to facilitate or encourage timely payments, including autopay and notifications; card issuers’ use of the late fee safe harbor provisions in Regulation Z; and card issuers’ revenue and expenses related to their domestic consumer credit card operations.
DATES: Comments must be received by July 22, 2022.
Click here to read the full NASCUS Summary (Member login required.)
It says users in the United States can expect digital asset services to come in the future.
 A subsidiary of the Huobi cryptocurrency exchange called HBIT Inc has received its Money Services Business (MSB) license from the United States Financial Crimes Enforcement Network (FinCEN).
A subsidiary of the Huobi cryptocurrency exchange called HBIT Inc has received its Money Services Business (MSB) license from the United States Financial Crimes Enforcement Network (FinCEN).
The Seychelles based Huobi said on Tuesday that the license creates a foundation for it to carry out crypto-related business in the U.S. in the future, as part of its strategic goals of “globalization and compliance.” The exchange is a major player, with more than $1 billion in volume in the past 24 hours, according to CoinGecko.
Before the great crypto crackdown by Chinese authorities, most Huobi users came from China, but according to the latest figures from Statista, most users in February 2022 originated from Russia and Ukraine.
The MSB license allows Huobi’s subsidiary to transmit money and operate as a fiat currency exchange, a required step by U.S. regulators to ensure FinCEN can monitor financial crimes such as money laundering.
However, it does not allow it to provide crypto-exchange services — which would require a money transmitter license. It says in the future, it expects to provide U.S. users with a compliant digital asset service.
Huobi said its subsidiaries in Hong Kong have also received asset management and securities advising licenses from the country’s Securities and Futures Commission.
The subsidiaries are also in the process of applying for a license to provide automated trading services and securities trading to become a fully compliant crypto-exchange in Hong Kong.
Huobi has been on a streak of licensing wins.
On June 21, the exchange won licenses in New Zealand and the United Arab Emirates. The latter was an Innovation License which, while not a trading license, allows it to access the local tech industry and get special tax treatment.
At the time, Huobi Group chief financial officer Lily Zhang told Cointelegraph it plans to receive its license to offer its full suite of crypto exchange services under Dubai’s Virtual Assets Regulatory Authority (VARA).
It hasn’t been all good news though, with the exchange’s Thai license revoked on June 16 after it reportedly failed to comply with local regulations. There are also rumors of significant staff layoffs and that its founder might be looking to exit the business.
Hong Kong-based crypto reporter Colin Wu reported on June 28 that Huboi intended to lay off up to 30% of its staff, with a later update on Saturday reporting rumors that Huboi founder Li Lin is looking to sell his 50% stake.
Courtesy of Jessee Coghlan, CoinTelegraph
BUREAU OF CONSUMER FINANCIAL PROTECTION [Docket No. CFPB–2022–0040] Federal Register Posting: Request for Information Regarding Relationship Banking and Customer Service
AGENCY: Bureau of Consumer Financial Protection.
ACTION: Request for information.
SUMMARY: The Consumer Financial Protection Bureau (Bureau or CFPB) is seeking comments from the public related to relationship banking and how consumers can assert the right to obtain timely responses to requests for information about their accounts from banks and credit unions with more than $10 billion in assets, as well as from their affiliates.
DATES: Comments must be received by July 21, 2022.
![]() Click here to read the full NASCUS Summary
Click here to read the full NASCUS Summary
(Member login required.)
 June 29, 2022 — When credit risk is on the rise, such as during an economic downturn, credit card companies may look at reducing consumers’ available credit limits to prevent against losses. Credit card line decreases are an industry practice where a company cuts a consumer’s credit limit on an existing account. A consumer’s available credit can disappear, sometimes without warning or subsequent explanation.
June 29, 2022 — When credit risk is on the rise, such as during an economic downturn, credit card companies may look at reducing consumers’ available credit limits to prevent against losses. Credit card line decreases are an industry practice where a company cuts a consumer’s credit limit on an existing account. A consumer’s available credit can disappear, sometimes without warning or subsequent explanation.
A new CFPB report describes how credit card companies increasingly used credit line decreases during both the Great Recession and at the start of the COVID-19 pandemic. Due to the critical role credit plays in financial resiliency, especially during a downturn, we sought to examine the importance and impact of these decisions by credit card companies.
The impact of limiting available credit lines
The following highlights our key findings:
Majority of decreased credit lines were not linked to recent credit card delinquencies
Credit line decrease actions were four times as common if a consumer had a recent credit card delinquency. However, approximately 67 percent of consumers who experienced declines in their credit line showed no evidence of a recent credit card delinquency.
For these consumers, the decision may be driven by other changes in their credit profile, internal account performance data, or by changes in institution risk management unrelated to their credit standing. Credit reports don’t currently indicate whether the action was driven by the consumer’s risk or the lender’s internal decision-making.
Credit line decreases led to dramatic reductions in available credit
Our research showed that line decreases resulted in a dramatic reduction in credit available on a consumer’s impacted credit card. For consumers across different credit score tiers, the median amount of credit decreased by approximately 75 percent. Median available credit was often reduced to less than $400 for all consumers except those with superprime credit scores (generally a superprime score is 720 or greater compared to deep subprime of 579 or less).
We also showed that a credit line decrease on a consumer’s highest balance card significantly affects a consumer’s total access to credit card lines. The impact of a line decrease may be more acutely felt for consumers in lower score ranges who are less likely to have as many cards as their prime counterparts and may find it more challenging to access new credit.
Rates of credit utilization went up
The credit utilization rate – or the amount of credit used against the available credit limit – also significantly increased, with most consumers essentially “maxing out” the card.
When their available credit decreased, median deep subprime, subprime, near-prime, and prime consumers reached 94 percent of their available credit. Even for super-prime consumers, their utilization rate more than doubled from 37 percent to 78 percent. We also showed that total combined utilization also increased after a credit line decrease for all but deep subprime scored consumers. This can have an impact on their credit scores – when utilization goes up, consumer credit scores tend to go down.
Credit line decreases tend to coincide with decreasing credit scores
Credit scores declined around the time of a line decrease, and this was felt by consumers of different credit scores. The decline, however, was significantly greater if a consumer had a recent credit card delinquency. During the analysis period, median credit scores for consumers with a recent card delinquency on any card decreased between 33 and 87 points. For consumers without a recent card delinquency on any card, median scores decreased between 1 and 12 points.
Credit balances remained depressed for subprime borrowers
While prime consumers may have used other credit cards or new accounts to offset the line decrease and return to previous total card balance levels, subprime and deep subprime balances remained depressed three quarters later, meaning that subprime borrowers are likely less able to return to previous card use.
This research is part of a series looking at consumer credit trends using a longitudinal sample of approximately five million de-identified credit records maintained by one of the three nationwide consumer reporting agencies.
Read the report, Credit Card Line Decreases .
Jun 30, 2022 — Central bank leaders warned Wednesday that inflation is going to last longer than some estimated.
Bitcoin fell toward $19,000 during Asian afternoon hours after central bankers renewed inflation warnings at the European Central Bank’s annual forum on Wednesday.
The asset dropped 5.5% in the past 24 hours, and is on track for a record 40% monthly decline. Other large cryptocurrencies also weakened, with ether dropping 9.9% in the past 24 hours and Solana’s SOL falling as much as 11%. Total cryptocurrency market capitalization fell 4.3%.
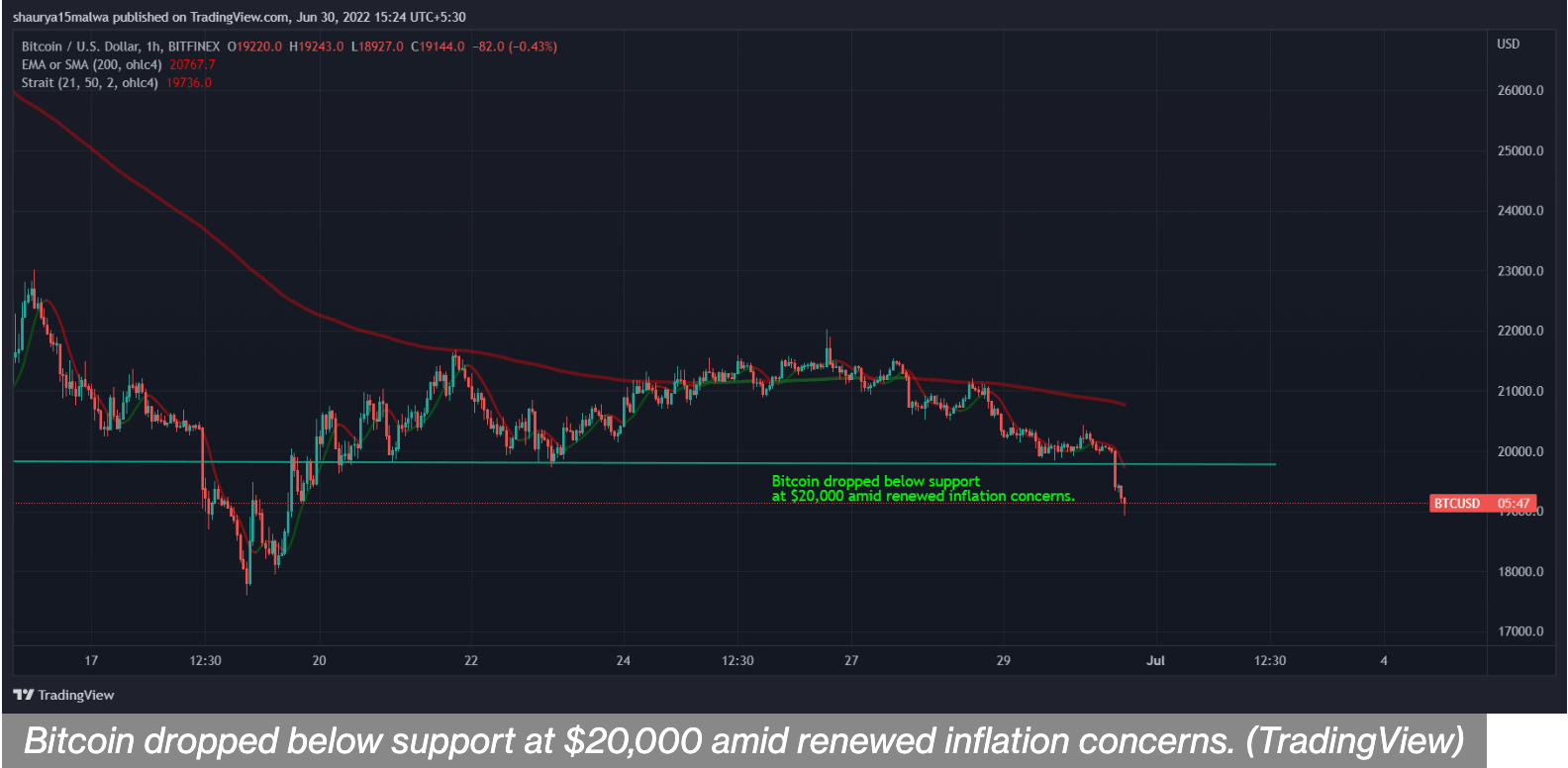
Federal Reserve Chairman Jerome Powell reiterated the central bank’s commitment to increasing interest rates to curtail inflation. Speaking at the ECB meeting, he said he was more concerned about the challenge posed by inflation than about the possibility of higher interest rates pushing the U.S. economy into a recession.
“Is there a risk we would go too far? Certainly, there’s a risk,” Powell said. “The bigger mistake to make – let’s put it that way – would be to fail to restore price stability.”
Powell said the Fed had to raise rates rapidly, Reuters reported, adding that a gradual increase could cause consumers to feel that higher prices of commodities would persist. About a week ago, his comments suggested rate hikes could soften before next year.
U.S. equity market futures fell following Powell’s comments, with S&P 500 futures dropping 1.59% and those on the tech-heavy Nasdaq 100 falling 1.9%. Asian markets were in the red with Japan’s Nikkei 225 declining 1.54% and the Asian-focused index Asia Dow falling 1.14%.
Central banks across the globe are weighing interest rate increases amid surging price pressures. Spain reported a 37-year record inflation of 10% earlier this week, while India and China are grappling with the risks of economic contraction.
Such concerns add to already critical selling pressure on bitcoin. The crypto has traded similarly to risky technology stocks in the past few months and has fallen 58% this year.
Contagion risks from within the crypto industry, such as the possible insolvency of crypto lenders and the blowup of prominent crypto fund Three Arrows Capital, have further caused downward pressure on the asset that was otherwise conceived as a potential hedge against inflation.
Courtesy of Dave Kovaleski, Financial Regulation News
June 20, 2022 — The Bank Policy Institute (BPI) offered feedback on the Securities and Exchange Commission’s (SEC) proposed climate disclosure policy, expressing its concerns.
The proposal would require public companies to provide a detailed financial accounting of climate-related risks, information on indirect emissions, and numerous requirements for disclosure of risk management policies and practices.
BPI officials said that many banks already voluntarily disclose climate information, adding that an overly prescriptive approach from the SEC could undermine the goal of providing useful information to investors. Further, BPI says the proposal fails to account for the interaction with the prudential bank regulatory framework.
“Banks share the SEC’s goal of communicating material climate risks transparently to investors and managing those risks in a prudent manner. However, the proposal’s overly detailed requirements would lead to a mountain of information that would be misleading and of little use to investors. This is particularly the case given the significant limits of climate data today. It is important to ensure that the climate-related disclosures produced are useful to investors,” Lauren Anderson, BPI senior vice president and associate general counsel, said.
While investors are increasingly seeking more information on how firms will be affected by climate-related risks, BPI says climate risk data is in the early stages of development. As such, there are significant data gaps and inaccuracies. BPI adds that data challenges are even more problematic for banks as they must rely on data from their clients to produce their climate disclosures. The approach that the SEC is taking could lead to a false sense of precision regarding climate reporting and end up misleading investors. Regulators should recognize the need for a flexible framework that will allow disclosures to improve over time.
Specifically, the proposal’s Regulation S-X financial reporting requirements are largely inoperable, will not result in useful disclosure for investors, and should be removed or, at a minimum, narrowed, said BPI.
Also, they state that the Scope 3 emissions disclosure requirements are overly broad as drafted and should be narrowed to focus on registrants’ material targets or goals. Further, the risk management aspects of the proposal should be modified so that they do not front-run, and are consistent with, ongoing efforts by the federal banking regulators.
In addition, the proposal’s board and management governance provisions should be modified to be less prescriptive and not place outweighed importance on one potential risk factor that public companies must manage. Among other recommendations, BPI says the proposal’s cost-benefit analysis likely under-estimates costs by several degrees and has not demonstrated the purported benefits outweigh even the identified costs. Also, BPI says the proposal should not require third-party attestation of Scope 1 and Scope 2 GHG emissions disclosures.
Jun 23, 2022 — Cornerstone and HCUA merger committees have begun the due diligence process.
The Cornerstone League and Heartland Credit Union Association are exploring the possibility of a merger. Both league boards approved moving forward with the due diligence process, and a letter of intent has been signed by both organizations. A merger between the two would create a five-state league serving up to 718 credit unions and 14 million members, led by Cornerstone League President/CEO Caroline Willard.
“We believe that the infrastructure supporting our credit unions must evolve to keep pace with the way credit unions and consumers have changed,” said Willard. “Partnering with Heartland can help both organizations do that.”
“Joining HCUA and Cornerstone together provides a unique opportunity for our leagues to maximize efforts in compliance and advocacy,” said Lisa Simmons, interim CEO at the Heartland Credit Union Association. “This partnership will provide all credit unions access to more options to better serve their members and communities.”
Willard said that in combining their shared strengths, Cornerstone and HCUA can help to preserve the unique role of financial cooperatives in the marketplace.
“By removing barriers on the federal, state, and local level, we can fight regulatory burdens more effectively and strengthen our influence as a larger regional league,” she said.
Cornerstone League Board Chairman James Boyd said that Cornerstone’s proven multi-state association model can be applied to create additional value in the Heartland region.
“We at Cornerstone are excited at the possibility of expanding our model—centralized professional staffing combined with boots on the ground in each state capital—into Kansas and Missouri,” said Boyd, who is also president/CEO of Abilene Teachers Federal Credit Union in Abilene, Texas. “Given the political and cultural similarities amongst our five states, we believe the combination can be smooth and productive.”
James Nastars, board chairman of the Heartland Credit Union Association and president/CEO of Meritrust Credit Union in Wichita, Kan., said the time is right to consider a merger.
“Our two associations complement each other in so many ways, and our focus and commitment to credit unions align very well,” he said. “By working together while still maintaining our individual state identities, it will create an even stronger league and provide our credit unions of all sizes with more opportunities to grow.”
Upon consolidation, both organizations would operate under the Cornerstone League brand, serving credit unions in Arkansas, Kansas, Missouri, Oklahoma, and Texas.
Following the due diligence process, the boards of both associations would need to vote on the approval of a merger agreement, and a vote of the members of both organizations would be required as well. In the meantime, members of both leagues will be invited to one of many townhall meetings to learn more about the consolidation, provide feedback, and ask questions. If the merger is approved, the tentative timeline for the merger to become official is Jan. 1, 2023.
Author: Cornerstone League
 One of the FDIC’s most important responsibilities is to prudently manage the Deposit Insurance Fund. The FDIC’s ability to credibly guarantee our nation’s insured deposits is vital for the stability of the banking system. The Deposit Insurance Fund has gone broke twice in the last 30 years.1 Just as large financial institutions should not expect a bailout from taxpayers, neither should the FDIC.
One of the FDIC’s most important responsibilities is to prudently manage the Deposit Insurance Fund. The FDIC’s ability to credibly guarantee our nation’s insured deposits is vital for the stability of the banking system. The Deposit Insurance Fund has gone broke twice in the last 30 years.1 Just as large financial institutions should not expect a bailout from taxpayers, neither should the FDIC.
The law requires the FDIC’s Board to establish and implement a restoration plan when the Deposit Insurance Fund’s reserve ratio falls below 1.35%.2 The plan must bring the reserve ratio back above the statutory floor within eight years. The fund’s reserve ratio breached the statutory floor on June 30, 2020. In the last six months, the situation has worsened, with the reserve ratio falling from 1.27% to 1.23%. The Deposit Insurance Fund is currently about $12 billion below the minimum prescribed by law. Given the serious risk of missing the statutory deadline, it is critical that the Board take steps now, while banking industry profits are robust. Otherwise, the Board may be forced to impose a larger rate hike later when economic conditions may be different.
I am voting in favor of shoring up the Deposit Insurance Fund by amending the restoration plan required by law and by proposing a small premium increase. These are important short-term actions.
Over the long term, I believe the Board should explore a new mechanism to automatically adjust premiums upward and downward based on economic conditions, rather than relying on ad-hoc actions. For example, calibrating assessment rates based on banking sector profitability, or a combination of metrics, is worth exploration. The Board should also evaluate the relative burden of assessments on banks of varying sizes, including whether the largest firms, especially global systemically important banks, should be paying a higher share of the assessments than they do today.
Regulators expect a bank board to actively monitor management’s execution of the bank’s objectives and require adjustments if warranted by changing conditions. That is sound governance. I am pleased we are demonstrating that we will hold ourselves to that same standard.
1. The Deposit Insurance Fund balance went negative in the early 1990s after the Savings and Loan Crisis and 1990-91 economic recession. The balance again went negative due to the 2008 financial crisis.
2. 12 U.S.C. 1817(b)(3)(B) and (E).
.
Join Us On October 19, 2022
Credit union board members, committee members, and management should not miss the North Carolina Executive Forum. We invite you to participate in this acclaimed, annual one-day session. Be sure to take advantage of this excellent training opportunity for directors and staff.
This is an in-person event.
Location
Goodwill Industries of the Southern Piedmont
5301 Wilkinson Blvd.
Charlotte, NC 28208
Room Name
Bank of America Room
Pricing
- $199 NASCUS Members & Carolinas Credit Union League Members (in-person)
- $299 Non-members (in-person)
Agenda
8:30 AM –– 9:00 AM Breakfast
9:00 AM –– 9:15 AM Opening Remarks by Dan Schline, President & CEO, Carolinas Credit Union and Rose Conner, Administrator, NC Credit Union Division
9:15 AM –– 10:15 AM Vendor Management with Frank Drake, Senior Counsel, Smith Debnam Narron Drake Saintsing & Myers, LLP
10:15 AM –– 10:30 AM Break
10:30 AM –– 12:00 PM Fraud (Credit Cards and Debit Cards) with Folashade Abiola-Banjac, Esq., Attorney, CLA
12:00 PM ––1 :00 PM Lunch
1:00 PM –– 2:00 PM Emerging Risk Outlook with Jim Bullard, Senior Consultant Risk & Compliance Solutions, CUNA Mutual Group
2:00 PM –– 2:15 PM Break
2:15 PM –– 3:15 PM NCUA Update with Jeanne Couchois, SVP Risk Management Resources, General Counsel, Carolinas Credit Union League
Can non-fungible tokens (NFTs) disrupt the lending market? And should credit unions, which are showing heightened interest in cryptocurrency, be entering this space as well?
Article courtesy of Ray Birch, CUToday.info
Lou Grilli, senior innovation strategist at PSCU, believes many credit unions will eventually answer “yes” to both questions, noting NFTs are already playing a part in the lending marketplace.
An NFT is a non-interchangeable unit of data stored on a blockchain, a form of digital ledger, which can be sold and traded, representing ownership of digital files such as photos, videos, and audio.
“So, an NFT could show you are the owner of a collectible, digital art, a song, a book, a video, or something more tangible, like tickets to a real-life event, or the title to a boat or to real-estate,” noted Grilli. “To understand how it works, think about owning a piece of a cryptocurrency coin, such as Ethereum. Your ownership of some amount of Ethereum is represented by a token on a blockchain. NFTs are likewise tokens on a blockchain, also representing ownership of something. Today, the most common use-case is ownership of artwork, like CrypotKitties, and characters in video games, such as Axie Infinity.”
The Coming Disruptor
But Grilli predicts NFTs will see more practical applications, such as real estate transactions, auto and boat titles, and other real-life uses.
“We already saw the first NFT-based real-estate transaction in the U.S. happen right here in Florida,” said Grilli. “And the person involved in this transaction has plans for several more.”
Where credit unions will first be forced to address NFTs is in mortgage lending, said Grilli.
“NFTs will be disrupters to mortgage lending,” he predicted. “Neobanks and crypto exchanges are entering the lending market by allowing clients to collateralize their digital asset holdings, meaning their holdings are locked up and can’t be sold or traded, in exchange for a loan.”
Recently, Genesis, a cryptocurrency exchange, offered a new client a six-month $1.25-million loan with a 7.5% interest rate—the equivalent of a 15% annual rate—collateralized by 10 NFTs by well-known digital artists Pak and Fewocious, valued at $5 million, Grilli pointed out.
“While this is an outsized example, there are firms like Arcade that in their first four months issued $10 million in similarly structured loans,” he said.
The New Card Perk
Grilli noted NFTs have already entered the credit card space as perks, suggesting they could disrupt those offerings, as well.
“AMEX is offering its cardholders a chance to purchase one of 14 unique digital images from a recent performance by R&B singer SZA as part of its rewards program,” Grilli said. “Amex is anticipating that NFTs will become more mainstream and will become an increasingly desirable perk for prospective customers. For credit unions, when it comes to crypto-savvy members, there will be a clear delineation of credit unions participating in the digital asset evolution—large and small—and those that are not.”
But when it comes to NFTs and payments cards, chargebacks may be a big issue, cautioned Grilli.
“Like gambling and other high-risk merchant category codes, chargebacks for NFT purchases pose a headache to issuers,” he said. “Due to the completely virtual nature of digital assets, it is even more attractive for a fraudster to use a stolen credit card number to purchase an NFT than it is to purchase a TV. Chargeback attempts due to friendly fraud, buyer’s remorse, kids using a parent’s card, occur with a much higher frequency in the digital world than in the physical world.”
Recognizing the potential for abuse in this area, Grilli noted that PayPal announced it would cap fraudulent claims about the sale of NFTs containing art, media or collectables at $10,000.
What to do Now?
What should credit unions be doing?
Grilli recommended monitoring member activity, “Ideally, using data analytics to track funds flowing. Every credit union should be tracking ACH and debit transactions to and from the major exchanges, such as Coinbase, crypto.com, Gemini, FTX, Binance, and BitFinex. Many credit unions would be surprised to see how much activity their members are already conducting in the world of digital assets. Likewise, credit unions should be looking at purchases made at the largest NFT exchanges, such as OpenSea, NFT Launchpad, crypto.com, and Rarible.”
Grilli pointed out that last summer Visa bought one of the NFT CryptoPunks for $150,000.
“Visa doesn’t consider this an investment, and the asset is not on their balance sheet,” Grilli said. “Visa believes that NFTs will play an important role in the future of retail, social media and entertainment. If this is an area of interest, start small, and have a team of enthusiasts go through the effort of buying an NFT, within a reasonable budget,” Grilli suggested.
Making it Count
Grilli believes credit unions will eventually have to make NFTs, and cryptocurrency, “count.”
“Digital assets as collateral,” he said. “Consider cryptocurrency balances, including NFT investments as part of a member’s ability to repay. Some members are starting to accrue significant balances in cryptocurrency and NFTs. When members start searching for a mortgage, they’d like their investment to be considered, I believe.”
What members don’t want to do is sell their cryptocurrency holdings, incurring a tax liability, and more importantly, abandoning the opportunity for additional gains on their investments.
“Likewise, they don’t want to sell their NFTs, given the limited market of buyers and the slower appreciation cycle,” he said.
Grilli pointed out neobanks are already working to attract new clients by recognizing crypto and NFT investments.
“They are using reasonable valuations, and then taking into account risks of loss, using these investments as part of the overall equation when underwriting a loan,” Grilli said.
As CUToday.info has reported, UNIFY Financial, Torrance, Calif., already plans to recognize cryptocurrency as collateral for a loan.
“While this may be something that not all credit unions are ready for just yet, loan officers should be following news related to the topic, discussing this with their chief compliance officer and NCUA examiner, and preparing for a future where digital assets, cryptocurrency, and NFTs comprise a growing portion of a household’s net worth,” Grilli said. “And this future looks like it might happen sooner than anyone expects.”
June 7, 2022 — Cyber attacks, hacking, and data breaches are a growing threat. Yet, many companies could have prevented these threats with a bit of risk management and a proactive approach to digital security.
Whether you’re going through a digital transformation or worried about data protection, these are the emerging cyber threats that you need to beware of.
A Forrester report showed that 94% of organizations suffered some type of cyber attack in 2020 alone. Even worse is that three-quarters of those attacks were due to a vulnerability caused by a technology put in place during the pandemic.
Data breaches cost businesses on average $4.24 million in 2021 [*]. And in breaches where remote work was a driving factor, the average cost was $1.07 million higher.
- Malware: a combination of the words malicious and software — is an umbrella term used to refer to software that damages computers, websites, web servers, and networks. While malware isn’t a new threat, hackers are constantly capitalizing on new approaches. This includes ransomware, viruses, spyware, and trojans. Once installed, malware can deny access to your network, secretly obtain sensitive data, and even destroy your system.
- Ransomware: is a type of malware that involves extortion. Hackers prevent users from accessing data, threatening to publish or delete it until a ransom is paid. Hackers take control of a victim’s computer when they click links or download attachments that contain malware.
- Cryptojacking: uses your computer to secretly “mine” cryptocurrencies such as Bitcoin and Ethereum. While not an immediate threat, it can slow down your devices significantly. Hackers use phishing emails or other methods to get you to click a link that then downloads the cryptojacking malware to your device.
- Viruses: are malicious pieces of code that damage your device and can replicate and spread between hosts. Much like flu viruses that can’t replicate without a host, computer viruses can’t spread without a host file or document. Once a virus successfully attaches to a host file or document, it can lay dormant until circumstances “trigger” it to execute its code. Once it does activate, the virus can spread across computers or even across corporate networks.
- Trojans: named after the famed Trojan horse, this type of malware uses helpful software as a backdoor to gain access and exploit a computer or network. Trojans are widely used to steal credit card information. Users click on a link that hides the Trojan malware or unknowingly download it along with legitimate software. Once the file is clicked and opened, the download proceeds to install malware onto the device.
- Worms: are self-contained malware that spread through other files and programs on their own. Unlike viruses which require a host, worms are standalone programs that can “wiggle” through your network. Worms are often sent through email attachments — they duplicate themselves and send a copy to all contacts in the hacked email list. Attackers can use worms to overload servers and achieve distributed denial of service (DDoS) attacks.
- Spyware: is a type of malware installed to collect information about users, including their system or browsing habits. There are several different types of spyware to beware of. For example, Infostealers steal your information from browser forms. While Keyloggers record your keystrokes to catch sensitive data. Spyware is distributed in many ways — links, phishing emails, pop-ups, infected ads, or even poisoned links on Google search.Once a user clicks on the link, their data is sent remotely to an attacker. The information is then used to blackmail the victim or install other malicious programs.
- Adware: displays unwanted ads on your computer. It can also change your browser homepage or even add unwanted plugins and other spyware. While adware isn’t quite a virus and isn’t as problematic as other code floating around the internet, you still need to remove it from your computer. Not only is it bothersome, but it could also cause other device issues down the line. Adware can come from either downloading it by mistake or getting it from a malicious website. Once it’s downloaded and installed, adware immediately starts tracking your web activity. One indicator that you’ve been infected is constant pop-up advertisements.
- Drive-By Downloads: are programs that install on your devices without your consent. These include bundled software and unintentional downloads of any files. Drive-by downloads often take advantage of apps, operating systems, software, or web browsers that haven’t been updated. They can use any website as a delivery method for corrupted files. Just like other malware, drive-by downloads enter your computer unintentionally. You don’t have to click on or download anything for your computer to be infected — it just happens when you visit an infected website.
- IoT Device attacks: Internet of Things (IoT) devices are common targets for bad actors as they don’t have space to run proper security systems and often store sensitive information like log-in details and passwords. Hackers exploit the weak security and constant connectedness of IoT devices to gain access to them. Once they install malware, hackers can link devices together and launch DDoS attacks. These attacks attempt to knock out networks by flooding them with traffic. IoT devices such as smart speakers can also act as a weak point in your network. Once hackers are in, they can gain access to your entire system.
- Wipers — or wiper malware: damage organizations by wiping as much data (if not all) as possible. Unlike ransomware which has financial motives, wiper attacks are purely disruptive. Criminals may also use wiper attacks to cover the tracks of separate data thefts.Wipers often target files, backups, and the system boot section. Normally, hackers override files to destroy them, but they don’t do this in wiper attacks because it’s time-consuming. Instead, hackers write a certain amount of data at intervals which destroys files randomly.
- Cross-Site Scripting (XSS): hackers insert malicious scripts into a website with the intent of stealing users’ identities through session tokens, cookies, and other information. The malicious code is usually JavaScript but can include Flash or HTML. XSS often occurs when users log onto a web application’s session. Victims unintentionally click on the content because they think it’s legitimate. But little do they know that the attacker altered the executed script, making XSS harmful and dangerous.
- Phishing: has been around for years, but is consistently one of the most common ways hackers try to scam you online. It involves sending messages that seem to be from a trusted source to gain personal information or scam you into downloading malware. Phishing attacks can occur via email, text (known as “smishing”), phone calls, fake websites, and social networks. Hackers use a combination of social engineering tactics to gain your trust. Then, they send messages containing malware or a link to a fake site designed to steal your information.COVID-19 scams (like PPP fraud) and phishing schemes have been especially prevalent in the past few years [*]
- Whale and spear phishing: is a phishing attack in which the prime targets are senior executives (aka the “big fish”). While spear phishing is a similar attack that hyper-targets a specific company or individual. In whaling, attackers impersonate high-level executives to try and steal sensitive data. In spear phishing, criminals research victims on LinkedIn or other social media sites and pose as a trusted source to gain access to their data.
- Pharming: is when cybercriminals capture user credentials through a fake landing page. There are two types of pharming: malware and DNS cache poisoning. Malware-based pharming uses trojan horses to direct you to a fake website. For example, you’ll get a link to enter your credentials on your banking site. But the link routes you to a fake (yet believable) landing page designed to steal your information. With DNS cache poisoning, hackers exploit your DNS server. So even if you enter the URL of your banking site, you’ll still be redirected to the fake website without your knowledge.
- SQL Injection Attacks: An SQL injection attack (SQLI) is typical in database-driven websites. SQL attacks happen when attackers inject code into a website or server database to steal money, change data, or erase web activity. Hackers find vulnerable website fields such as contact forms and insert malware. Once the SQL query is inserted into the website, the attacker can execute malicious commands on the database.
- Denial of Service (DoS): is a website attack where attackers overwhelm a system or network with internet traffic. A variation of DoS attacks is the distributed denial of service (DDoS) attacks. With DDoS attacks, hackers infect computers on the network with malware to turn them into bots. Attackers control the bot network (or botnet) by sending instructions remotely. Some hackers even use artificial intelligence (AI) technologies for automation purposes. DDoS attacks result in a server overflow or network error. It can be challenging to separate DDoS traffic from regular traffic.
- Brute Force Attacks: are a type of cryptographic attack where hackers use software to repeatedly guess your login credentials. One in five networks have experienced a brute force attack.Hackers attempt to access an account by trying different passwords until they guess the right one. When you’re against hackers with a powerful computing engine or control over an extensive botnet, it can pose a problem. Some warning signs that you’re under a brute force attack include:
- The same IP address trying to log in multiple times.
- Many IP addresses try to log into a single account.
- Multiple unsuccessful login attempts being made from different IP addresses in a short period.
- Man-in-the-Middle Attacks (MitM): are a type of “shoulder surfing” where hackers eavesdrop on your connection. Hackers intercept data transfers between a server and a client to steal data and manipulate traffic. Attackers insert themselves through an IoT device or exploit unsecured public Wi-Fi.
- Insider Threats: are security risks that begin within the targeted organization. It often involves a current or former employee with administrator privileges or access to sensitive information. Insider threats have increased by 47% over the last two years [*], making them an emerging cyber threat. Insider threats occur when someone with authorized access misuses their access. Insider threats can be intentional or unintentional. Unintentional threats occur when a negligent employee falls victim to malware or phishing scams. Most security operations focus on external threats. But the best course of action for limiting insider threats is restricting employee access to systems they need for work.
- Zero-Day Attacks: Zero-day attacks happen to websites with newly-discovered security vulnerabilities.The term ‘zero-day’ alludes to web developers recently discovering the flaw, which means they have had zero days to fix it. Attackers jump to take advantage of the small time frame in which the device or program is vulnerable. Preventing zero-day attacks requires constant monitoring and proactive detection.
Read more about these threats with real-life examples here.
Courtesy of Christopher Bray, Aura
 Urges Financial Institutions to Aid in Combatting Growing Threat
Urges Financial Institutions to Aid in Combatting Growing ThreatThe Financial Crimes Enforcement Network (FinCEN) is issuing an advisory to alert financial institutions to the rising trend of elder financial exploitation (EFE). EFE involves the illegal or improper use of an older adult’s funds, property, or assets, and is often perpetrated either through theft or scams. The advisory highlights new EFE typologies and red flags since FinCEN issued its first advisory on the issue in 2011.
“FinCEN is proud to support World Elder Abuse Awareness Day and call attention to a concerning and tragic rise in elder financial exploitation. Older adults should not have to endure abuse by criminals who seek to defraud them of their lifelong savings, or who wish to lure them into scams or schemes under false pretenses,” said FinCEN Acting Director Himamauli Das. “Financial institutions serve on the frontlines in protecting their older customers’ finances, and can play a critical role in helping to identify, prevent, and report suspected elder financial exploitation. Financial institutions’ vigilance matters. Their reporting matters.”
In 2021, financial institutions filed 72,000 Suspicious Activity Reports (SARs) related to EFE. As referenced in the advisory, this represents an increase of 10,000 SARs over the previous year’s filings. The Consumer Financial Protection Bureau (CFPB)’s estimate of the dollar value of suspicious transactions linked to EFE has similarly increased—from $2.6 billion in 2019 to $3.4 billion in 2020. This is the largest year-to-year increase since 2013.
FinCEN’s EFE advisory highlights behavioral and financial red flags to aid financial institutions with identifying, preventing, and reporting suspected EFE. In line with the risk-based approach to compliance with the Bank Secrecy Act, financial institutions should perform additional due diligence where appropriate and remain alert to any suspicious activity that could indicate that their customers are perpetrators, facilitators, or victims of EFE.
In addition to filing a SAR, FinCEN recommends that financial institutions refer their older customers who may be victims of EFE to the Department of Justice’s National Elder Fraud Hotline at 833-FRAUD-11 or 833-372-8311 for assistance with reporting suspected fraud to the appropriate government agencies. For educational resources on EFE and scams targeting older adults, please see the CFPB’s Office for Older Americans.


