By Mary K. Pratt, CSO Magazine
Click here to read the entire article.
Insiders have always posed a risk, but modern technologies, tactics, and motivations have increased the threat, likelihood, and consequences of insider-related incidents.
Insider threats are coming back in a consequential way.
According to the State of Human Risk Report from Mimecast, 42% of organizations have experienced an increase in malicious insider incidents over the past year, with 42% also reporting a rise in negligent incidents for the first time.
The report further found that organizations experienced an average of six insider-driven incidents per month at an estimated cost of $13.1 million per incident. Additionally, 66% of the 2,500 surveyed IT security and IT decision-makers expect insider-related data loss to increase over the next 12 months.
“Insider risk has become one of the most consequential and underestimated threats facing organizations today, not just because of the data loss it causes, but because attackers are increasingly exploiting insiders as a deliberate entry point to bypass perimeter defenses entirely,” Mimecast CISO Leslie Nielsen said in announcing his company’s research results.
“The data shows both careless mistakes and deliberate actions driving incidents in equal measure,” he added. “Rather than trying to manage human behavior, organizations need adaptive controls that identify high-risk actions and adjust protections in real-time, creating friction when someone accesses data they shouldn’t, regardless of whether they have valid credentials. As AI makes it easier for insiders to exfiltrate data at scale, security must meet users at the point of risk.”
The state of insider threats today as technologies, tactics, and motivations evolve
Insider threats continue to fall into two broad camps. On one side is the malicious insider who knowingly acts with the intent to harm. On the other side is a member of the organization whose impacting actions may be accidental or negligent, or in some cases manipulated by a malicious outsider.
Click here to continue reading.
By Orrick, Herrington & Sutcliffe LLP/JD Supra
On March 13, the U.S. Court of Appeals for the 10th Circuit denied a petition for rehearing en banc in a case challenging the court’s earlier decision upholding the Fed’s authority to deny master account applications to eligible state-chartered banks (previously covered by InfoBytes here). Three judges voted to grant rehearing, while the remaining five non-recused judges on the court voted to deny.
A dissent joined by one other judge argued that the DIDMCA requires the Fed to provide access to services to all eligible nonmember depository institutions, and, because access to services requires a master account, every nonmember is eligible for a master account. The dissent noted that the panel’s decision endorsing “unreviewable discretion” effectively hands the Fed a veto over states’ chartering power.
The dissent further warned that the majority’s decision does not align with the notion that, where the statute is ambiguous, it must be interpreted to avoid creating a constitutional problem. By allowing unappointed regional Fed officials with “unreviewable discretion” to deny master accounts, the dissent contended such officials wield significant authority pursuant to the laws of the United States, making them “officers” in the constitutional sense, raising serious constitutional concerns because the appointments process for such officials does not comport with procedures under the Appointments Clause.
The dissent also highlighted the case’s importance, citing its consequences for the financial services industry.
Muhammad Zulhusni, AI News
Click here to read the entire article.
AI agents are starting to take on a more direct role in how financial advice is delivered, as large banks move into systems that support client interactions.
Bank of America is now deploying an internal AI-powered advisory platform to a subset of financial advisers, rolled out to around 1,000 financial advisers, according to Banking Dive. The move is one of the clearer early examples of how AI is being used in core banking roles, where systems support decision-making in real time.
The platform is based on Salesforce’s Agentforce, which enables the creation of AI agents to handle tasks. It is designed to help advisers handle client queries and prepare recommendations. It can also help manage daily workflows. According to Banking Dive, the system is part of a wider push among major banks to test how AI agents can work alongside human staff.
Bank of America has been expanding its use of AI in its business. It’s said its virtual assistant Erica handles work equivalent to about 11,000 employees, while 18,000 software developers use AI coding tools that have improved productivity by around 20%.
AI agents move to financial decision-making
The approach differs from earlier deployments of AI in banking, which focused mainly on chatbots or internal productivity tools. In those cases, AI was used to answer simple questions or automate routine tasks. The newer systems are built to handle more complex work, including analysing client data.
Firms like JPMorgan, Wells Fargo, and Goldman Sachs are also testing AI tools aimed at improving productivity and helping staff in client-facing roles, though these efforts vary and are not always focused on advisor-specific AI agent systems. While each bank is taking a different approach, the common goal is to increase output without expanding headcount.
Banks report gains in how quickly advisers can access information or prepare for meetings, based on industry reporting and early deployment feedback. Yet there are ongoing concerns about accuracy and oversight, especially when AI systems are used to suggest financial decisions.
Click here to continue reading.
By PYMNTS.com
Click here to read the entire article.
The never-ending battle against payments fraud is entering a more complicated phase as artificial intelligence (AI) allows criminals to replicate human activity with unsettling accuracy.
Voices can be synthesized, identities can be fabricated from fragments of real data and automated programs increasingly behave like legitimate customers moving through digital channels.
Those developments are creating new vulnerabilities across financial services and especially insurance payments, according to Kevin Ostrander, chief revenue officer at digital insurance platform One Inc.
Insurance payment systems face particular exposure because they manage both premium payments and claims disbursements. Fraud attempts may involve automated scripts testing card numbers, bots probing payment systems or criminals attempting to access policyholder accounts.
“AI is causing a great challenge around traditional identity checks by mimicking human behavior at unprecedented scale,” Ostrander said during a “What’s Next in Payments” interview with PYMNTS. “We’re seeing fraudsters that are using AI to create synthetic identities that pass basic verification processes.”
Synthetic identities often combine stolen financial information with fabricated personal details. When those identities are convincing enough to pass traditional verification checks, fraudsters can open accounts, access sensitive information or initiate payments that appear legitimate.
“There’s a hyper focus in the industry right now on measuring and detecting anomalies in behavior and data patterns that really ensure even the most sophisticated synthetic identities are flagged and checked before any basic verification process takes place,” Ostrander told PYMNTS.
Fraud That Looks Like Normal Behavior
While fabricated faces and cloned voices draw attention, Ostrander said the most troubling development is the rise of automated behavior designed to imitate legitimate customers.
“Fake faces and fake voices are alarming, but the fake normal behavior is the most concerning and rapidly growing threat,” he said.
AI systems can now reproduce browsing habits, transaction patterns and conversational responses that resemble ordinary customer activity. Because those interactions resemble authentic behavior, the signals of fraud are far less obvious.
To detect those activities, payment providers increasingly analyze how users interact with digital interfaces.
Spotting bots often requires monitoring factors such as transaction speed, mouse movements, navigation patterns and device characteristics. Combined with systems that detect automation or device spoofing, those signals can help distinguish a legitimate policyholder from an automated program attempting to impersonate one.
Click here to continue reading.
By Emily Claus, CUSO Magazine
Click here to read the entire article.
Odds are, in the last few years you have received a spam text or email supposedly from reputable companies such as Apple and Amazon. These texts or emails were probably claiming you owed them a certain amount or that there was an issue with your account that could all be solved if you clicked on the very suspicious link they included.
These tricks have become fairly well known and easy to spot. The messages often contain misspellings or odd grammar, the URLs and links they provided only vaguely resembled the actual company they claimed to be from, and should you dare to click on the link, the website would most likely look a little off. For many, these texts were probably easy to spot as fake, delete, and move on from. No big deal.
Text scams are on the rise
Yet, despite the shortcomings in these earlier iterations of the scam, many still fell for them. The number of times I received a panicked call from my parents or grandparents because they were worried they somehow owed Apple $537.19 and weren’t sure how it could have happened and could I please help them look at their Apple transactions, is more than one might like to think. Even my younger more tech-savvy friends have fallen—or nearly fallen—prey to such scams.
In fact, according to the Federal Trade Commission, from July 2020 to June 2021, Amazon scammers alone had increased more than fivefold and managed to steal over $27 million from Americans.
These scams are not limited to Amazon either. Often, these bad actors will pose as the victim’s bank or credit union and lead them to a copy of your online banking website to trick them into sharing their credentials. While this trick is not exactly “new,” the method and execution behind it have reached a near-perfect level.
Click here to continue reading.
By Anjali Gopinadhan Nair, CSO Magazine
Click here to read the entire article.
Scary news: Hackers aren’t “breaking” your MFA anymore — they’re just riding shotgun during your login to steal the session token right out from under you.
Multi-factor authentication was supposed to be the solution. For years, security teams have told employees that MFA would keep them safe. Password stolen? No problem — attackers still need that second factor.
But adversary-in-the-middle (AiTM) phishing has changed everything. These attacks do not try to steal passwords and MFA codes separately. They capture the entire authentication flow in real time, including the session token that proves a user is logged in. The employee does everything right — checks for HTTPS, verifies the MFA prompt, avoids suspicious attachments — and still gets compromised.
This should concern every security leader. If our training, our MFA and our security awareness programs cannot protect someone who is genuinely trying to be careful, then what exactly are we promising when we tell users MFA will keep them safe?
Why this is not the phishing you trained for
Traditional phishing meant sloppy fake login pages with typos and dodgy URLs. Those pages could not handle MFA because they had no connection to the real authentication service.
Here is what changed, and I wish more security leaders understood this: modern phishing pages are not fake. They are proxies.
Tools like Evilginx sit between the user and the legitimate service — Microsoft, Google, Okta, whatever — and relay everything in real time. The employee types their password. It goes to Microsoft. Microsoft sends the MFA challenge. It flows back through the proxy to the employee’s phone. The employee approves it. The session cookie — that golden token proving authentication — passes right back through the proxy into the attacker’s hands.
Click here to continue reading.
By Tara Payne and Drew Ruben, Bank Policy Institute
Click here to read the entire article.
Americans’ savings are at risk as never before as new, technology-driven fraud and scams are surging across the U.S, costing American households an estimated $12.5 billion in 2024, a 25 percent increase over the previous year. These are just reported losses, with actual totals likely much higher. Using sophisticated technology, scammers are directly targeting unsuspecting consumers, and there’s no better route to a consumer than through their phone and its apps.
Scammers rely on social media channels and communication networks to reach customers. According to a recent Aspen Institute report, 68% of Americans reported receiving scam calls at least weekly, 61% of Americans reported receiving scam text messages at least weekly and about one-third of Americans say they get scam phone calls at least daily. These statistics are alarming and demonstrate that current policies for addressing fraud are insufficient. And while financial institutions are doing their part to educate consumers and mitigate incidents of fraud, by the time fraud reaches the banks’ systems, consumers may have already been harmed and their funds put at risk. As a result, action from industries and regulatory bodies outside of the banking sector is needed to achieve a durable solution.
The Problem and the Solutions
Phone scams have become part of everyday life for American consumers, and they’re becoming more sophisticated and convincing, boosted by AI deepfakes, voice cloning and location spoofing. Many scams originate from organized transnational crime groups that leverage global communications infrastructure to target Americans at scale.
In this global piracy enterprise, the FCC’s task is to safeguard the ports of entry and regulate the highways upon which data travels. Helpful steps would include: mandating standards for authenticating all U.S. calls; alerting consumers to unauthenticated calls and messages, especially international ones; deploying robust international anti-scam filters to block spoofing and mass campaigns; enforcing anti-fraud standards consistently across mobile virtual network operators; and sharing confirmed scam numbers and traffic data across carriers.
Click here to continue reading.
By PYMNTS Data Books
Click here to read the entire article.
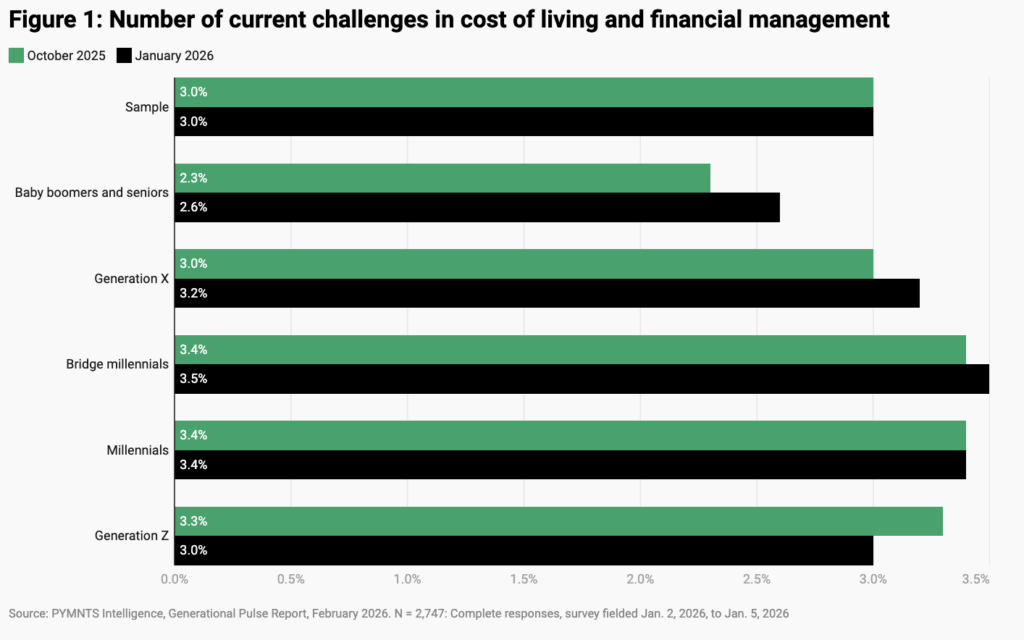
New PYMNTS Intelligence research reveals that younger households are juggling multiple bills, deploying more coping strategies and facing growing family-related costs during their peak earning years. Yet even as millennials work harder to manage their finances, their confidence that strategies are working is slipping.
Millennials, born between 1981 and 1996 and now age 30–45, are navigating a cost-of-living environment that has ceased spiking and cooling to stay persistently high. In this Data Book, these consumers (including bridge millennials, born between 1978 and 1988 and now age 38–48) stand out for the number of overlapping financial pressures they face, the number of tactics they use to cope and how quickly their confidence in those maneuvers is eroding.
Five Millennial-Centered Data Points
Cost Pressures
Millennials report an average of 3.4 simultaneous cost pressures, while baby boomers and seniors report 2.6. Financial management for this younger generation increasingly involves juggling multiple bills rather than solving a single problem.
Grocery Squeeze
Grocery stress for millennials rose 11 percentage points from October to January, increasing from 79% to 90%. For these consumers, even routine spending now requires active day-to-day tradeoffs.
Click here to continue reading.
By Howard Solomon, CSO Magazine
Click here to read the entire article.
HR staff need to understand that these unfamiliar files execute commands and shouldn’t be opened.
Threat actors are still having success tricking human resources staff into opening malware-infected phishing emails.
The latest example is detailed by researchers at Aryaka, who this week described a campaign by an unnamed threat actor who is distributing resumés containing a malicious ISO file to HR departments. It’s delivered through recruitment channels, and hosted on what an employee, or an email gateway’s filters, would see as trusted cloud infrastructure.
When the victim mounts the ISO, which is an archive of an optical disc such as a DVD, and opens its contents, a malicious shortcut (.lnk) is executed, launching obfuscated PowerShell commands that extract hidden payloads embedded within a steganographic image. A malicious DLL is then sideloaded using a legitimate signed application, allowing the attacker’s code to run under the guise of trusted software. The goal is to harvest data from the infected computer.
The malware’s most alarming feature, says Aryaka, is an internal module dubbed BlackSanta which shuts down endpoint detection and response (EDR) agents that would detect this attack. It deploys a Bring-Your-Own Vulnerable Driver (BYOVD) technique that loads legitimate but exploitable kernel drivers, gaining low-level system access, then systematically turns off security tools.
Click here to continue reading.
By Dave Kovaleski, Financial Regulation News
The Federal Reserve Board is seeking public feedback on a proposal to codify the removal of reputation risk from its supervision of banks.
The proposal reiterates the Fed board’s policy against penalizing or prohibiting an institution from banking a customer engaged in legal activity.
“We have heard troubling cases of debanking—where supervisors use concerns about reputation risk to pressure financial institutions to debank customers because of their political views, religious beliefs, or involvement in disfavored but lawful businesses,” Federal Reserve Vice Chair for Supervision Michelle Bowman said. “Discrimination by financial institutions on these bases is unlawful and does not have a role in the Federal Reserve’s supervisory framework.”
In June, the board announced that reputation risk would no longer be a component of examination programs in its supervision of banks.
This new proposal would build on that announcement to help ensure supervisory decisions are based on material financial risks. It also seeks to increase clarity and facilitate greater precision in supervisory decision-making. Further, it would support the Board’s focus on core financial risk in its supervision of banks.
However, this change does not alter the board’s expectation that banks maintain strong risk management to ensure safety and soundness and compliance with law and regulation.
Comments are due within 60 days after publication in the Federal Register.
By Sherry Virden, CreditUnions.com; This is part of the Callahan Financial Performance Series.
Click here to read the entire article.
The nationwide affordability crisis has become an inescapable issue for credit union members, affecting how they borrow, spend, and plan for the future.
From housing and vehicles to education and everyday essentials, the cost of daily living is on the rise, leaving many households struggling to save, qualify for loans, and manage debt.
In today’s economy, it is essential that credit unions balance member support with sustainable lending practices that ensure continued operations for those in need.
Housing Prices Reposition The Real Estate Portfolio
Housing prices are climbing faster than wages in many regions, and members are struggling to save for down payments, qualify for mortgages, or comfortably manage monthly payments if they do buy.
At the same time, other residential real estate products — namely HELOCs — have surged. Existing homeowners are increasingly tapping equity for not only home improvements but also to pay down student loans, consolidate high‑interest debt, and cover unexpected expenses.
New Pressures Drive New Lending Plays
Higher sticker prices, rising interest rates, and longer loan terms mean monthly car payments now consume a larger share of already-strained household budgets for longer.
Considering the affordability concerns with new cars, used auto — traditionally the more budget-friendly option — remains the dominant vehicle loan. However, even the average used car loan balance has increased 3.0% at credit unions since last year, suggesting new loans for used auto are larger than they used to be. That can be a major barrier for members in need of new transportation.
Click here to continue reading and view the corresponding graphs.
By Frank Diekmann, CU Daily
Click here to read the entire article.
John Crews, deputy assistant secretary for financial institutions policy in the Treasury department, has emerged as the leading candidate to be nominated to the NCUA board and replace the departing Kyle Hauptman, sources have told the CU Daily.
Crews was appointed to the position in mid-2025 and has a long history in Washington. Prior to joining the Treasury Department, he served as a policy advisor to Majority Leader Rep. Steve Scalise (R-LA), where he covered economic and financial services policy, and prior to that was the policy director of the Senate Banking Committee.
During the first Trump Administration, he served on the National Economic Council as a special assistant to the President for Economic Policy. Crews, who has held numerous other positions as a staffer on the Hill going back a decade, is a graduate of Princeton University with a BA in politics.
In September, Crews and Hauptman were on the same agenda for a Hike the Hill event hosted by the League of Credit Unions, where Crews appeared as part of a “fireside chat.”
The NCUA board currently has one member, Chairman Kyle Hauptman, who is waiting to exit after the Securities and Exchange Commission announced he has been appointed to the Public Company Accounting Oversight Board (PCAOB).
Hauptman, whose term expired in August of 2025, has said he would remain on the board until a successor could be nominated and approved by the Senate. Credit union advocates on Capitol Hill have said they do not believe Hauptman’s appointment would have been announced were a successor not in the works.